Introducing Container Image Scanning
Table of Contents
Container images are a popular way to package and deploy applications. These are the deployable artifacts in modern cloud native world. However, they often contain vulnerabilities and malicious packages. Conventional container image scanning tools focus on vulnerability (CVE) identification for container images. However, malicious or compromised packages do not have CVEs. To protect against the risk of vulnerabilities and malicious packages, deployable container images must be evaluated for security risks. vet now supports scanning container images using --image flag.
Scanning Local Images
Container images available in local docker server catalog can be scanned using the following command:
vet scan --image redis:latestScanning Remote Images
vet will pull the image data if the container image is not available in local docker server catalog.
vet scan --image redis:latestScanning Local Tarballs
Exported container images can be scanned using the following command:
vet scan --image /path/to/image.tarThis tarball can be created using docker save command. This is useful when you want to scan a container image that is not available in local docker server catalog.
docker save redis:latest -o image.tarMalicious Package Scanning
Container scanning can be combined with malware detection using the --malware flag. It also supports various reporting formats including --report-cdx and --report-json for generating standardized output.
vet scan --image redis:latest --malwarevet scan --image redis:latest --report-cdx=report.cdx.jsonPolicy Driven Container Scanning
vet is designed as policy first. It uses a Common Expression Language based policy engine to allow flexible policies. For example, to prevent containers with malware or critical vulnerabilities from getting deployed, you can run vet with the following policy:
vet scan --image redis:latest --malware --filter 'vulns.critical.exists(p, true)' --filter-failNote: vet will always fail when a malicious package is detected.
Other scanning options
For more details on how to use vet with container scanning, please refer to the documentation.
Demo
Bugs and Feedback
Found a bug or have suggestions? We’d love to hear from you! Please open an issue in our vet GitHub repository. For discussions about vet and other SafeDep tools, join our friendly developer community on Discord. We’re always excited to connect with fellow developers and hear your thoughts!
- container-scanning
- malware
- security
Author
Kunal Singh
safedep.io
Share
The Latest from SafeDep blogs
Follow for the latest updates and insights on open source security & engineering
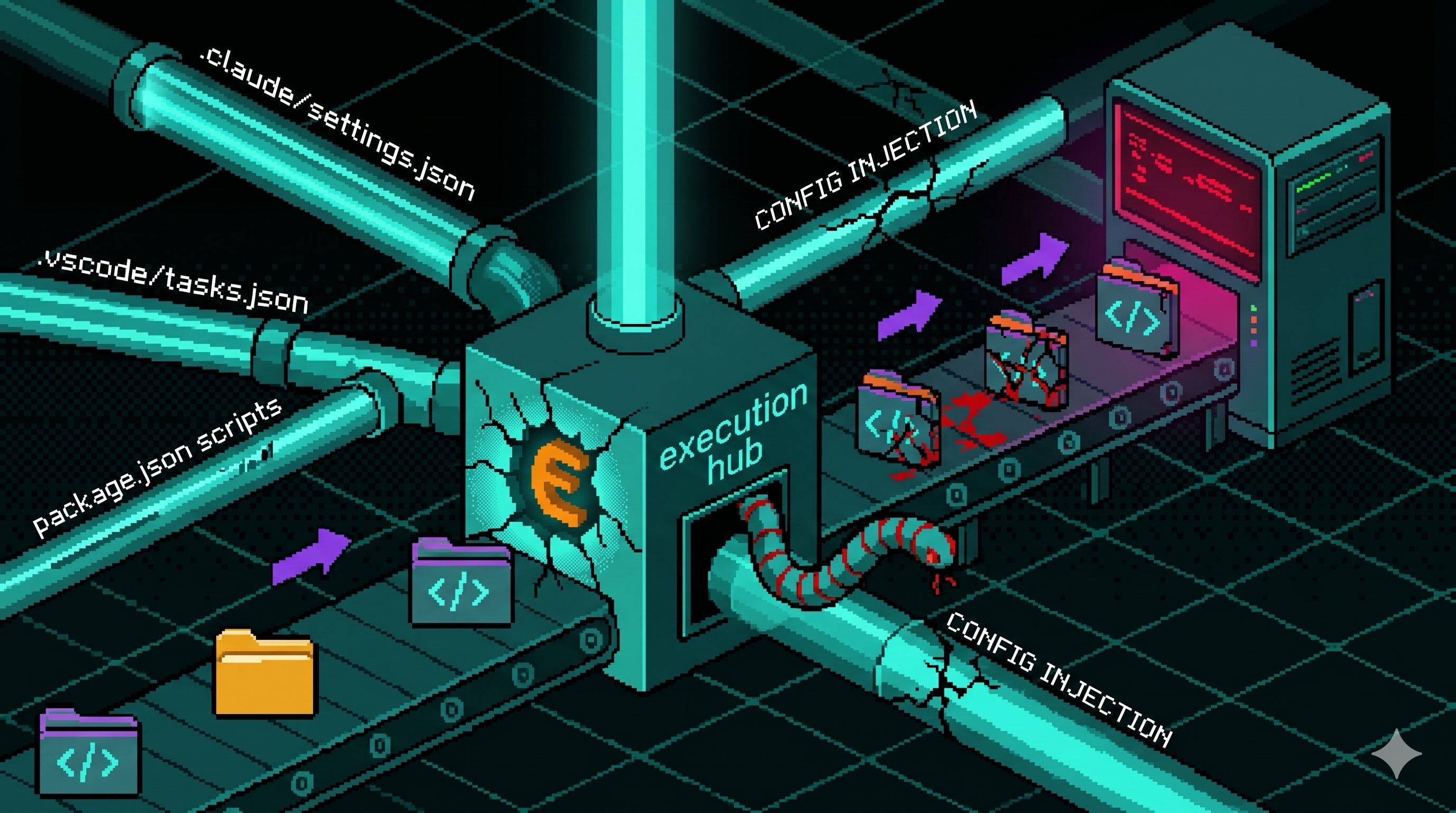
Config Files That Run Code: Supply Chain Security Blindspot
Editor and package-manager config files auto-execute commands when a developer opens a folder or installs dependencies. The Miasma worm wired one dropper into seven of them across Claude Code,...
Axios Typosquats Deliver the Epsilon Stealer
Two axios typosquats on npm, turbo-axios and faster-axios, form a campaign delivering Epsilon Stealer through a four-stage chain. The Electron infostealer grabs browser credentials, crypto wallets,...

Miasma Worm Targets AI Coding Agents via GitHub Repos
A Miasma worm variant injects a 4.3 MB dropper into GitHub repos across multiple maintainers, wiring it to auto-run through Claude Code, Gemini, Cursor, and VS Code config files. No npm package is...
Mini Shai-Hulud "Miasma: The Spreading Blight" Hits @redhat-cloud-services: Multiple Packages at Risk
The attacker compromised the @redhat-cloud-services GitHub Actions OIDC trusted publisher to ship [email protected] with a Mini Shai-Hulud worm. The same publisher controls 32 packages across the...

Ship Code.
Not Malware.
Start free with open source tools on your machine. Scale to a unified platform for your organization.

