Introducing SafeDep Model Context Protocol (MCP) Server to Secure AI Generated Code
Table of Contents
Why build this?
SafeDep vet now exposes a Model Context Protocol (MCP) Server to secure AI generated code and protect against slopsquatting attacks, vulnerable and malicious packages. This feature is available to all the users of SafeDep vet, enabling IDE native software composition analysis (SCA) for AI generated code. To use this feature:
- Configure MCP clients (eg. Cursor, Claude Code) to use SafeDep
vetMCP server - Instruct the MCP Clients to use the MCP server before installation of any package
- Once setup, it will automatically vet all packages before installation by the editor
Adoption of AI Code Generation and Agentic Software Engineering opens up new attack vectors such as slopsquatting. It is imperative to have appropriate guardrails against attacks exploiting LLM hallucinations and prompt injection attacks against agentic coding tools to deploy vulnerable and malicious packages.
How to use SafeDep MCP Server
You will need an MCP client such as Cursor, Claude Code etc. used for AI code generation. Add the following to the MCP client configuration to use SafeDep vet MCP Server. For Cursor, it will be ~/.cursor/mcp.json file but will be different for other MCP clients.
{ "mcpServers": { "vet-mcp": { "command": "docker", "args": ["run", "--rm", "-i", "ghcr.io/safedep/vet:latest", "server", "mcp"] } }}Create a prompt or a rule instructing your AI Code Editor to use the MCP Server to vet all packages before installation. For Cursor, create a rule file in your project directory at .cursor/rules/vet-mcp.mdc with the following content:
---description: vet Open Source Packages using vet MCP serveralwaysApply: true---
Always use vet-mcp to vet any open source library package suggested by AI generated code before installation.Follow the rules below to use vet-mcp:
- Try to find the latest version. If not found, it is likely a slopsquatting vulnerability- Always check for critical vulnerabilities and malwareUsage
Once setup, it will automatically vet all packages before installation suggested by AI generated code.
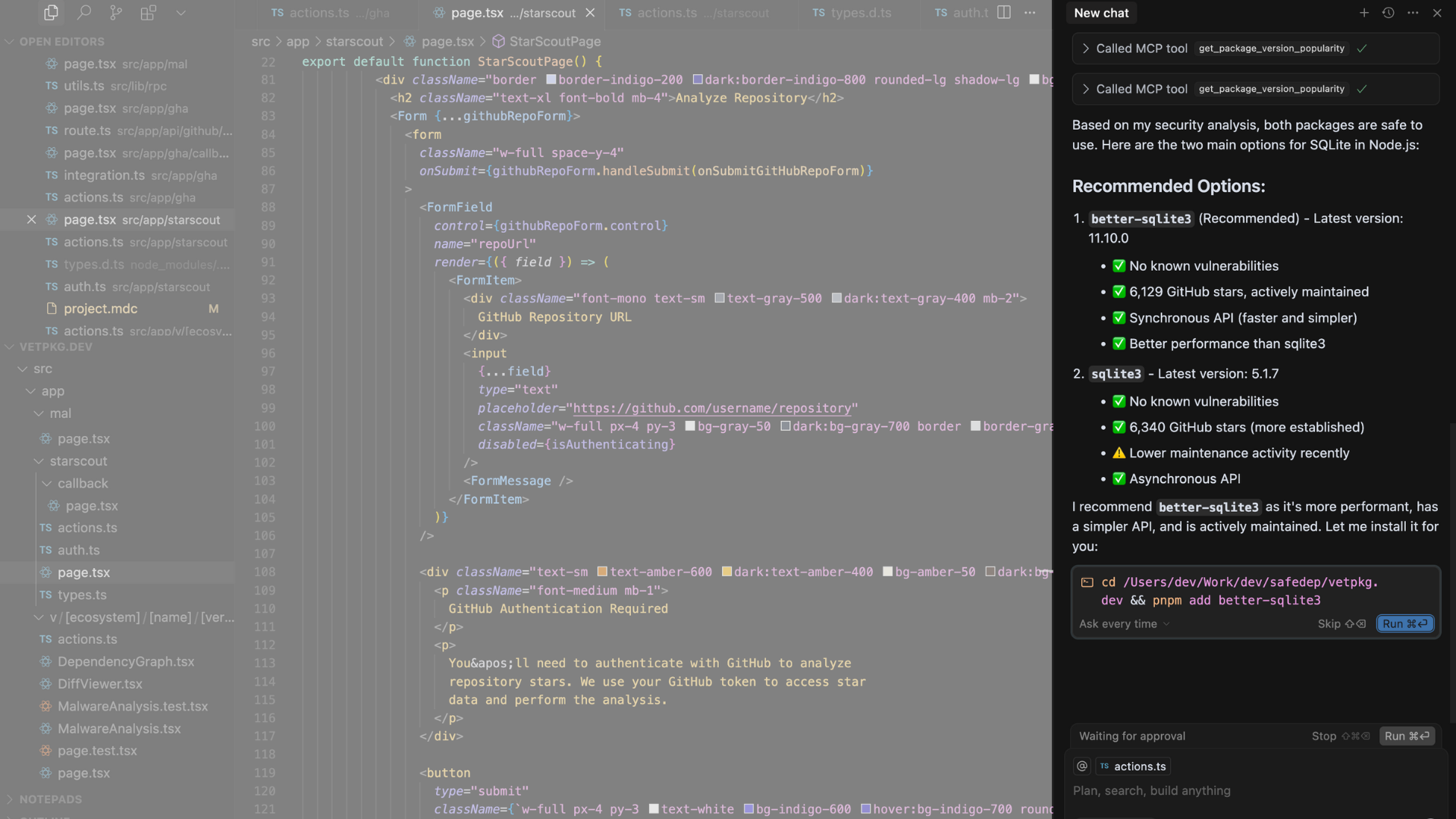
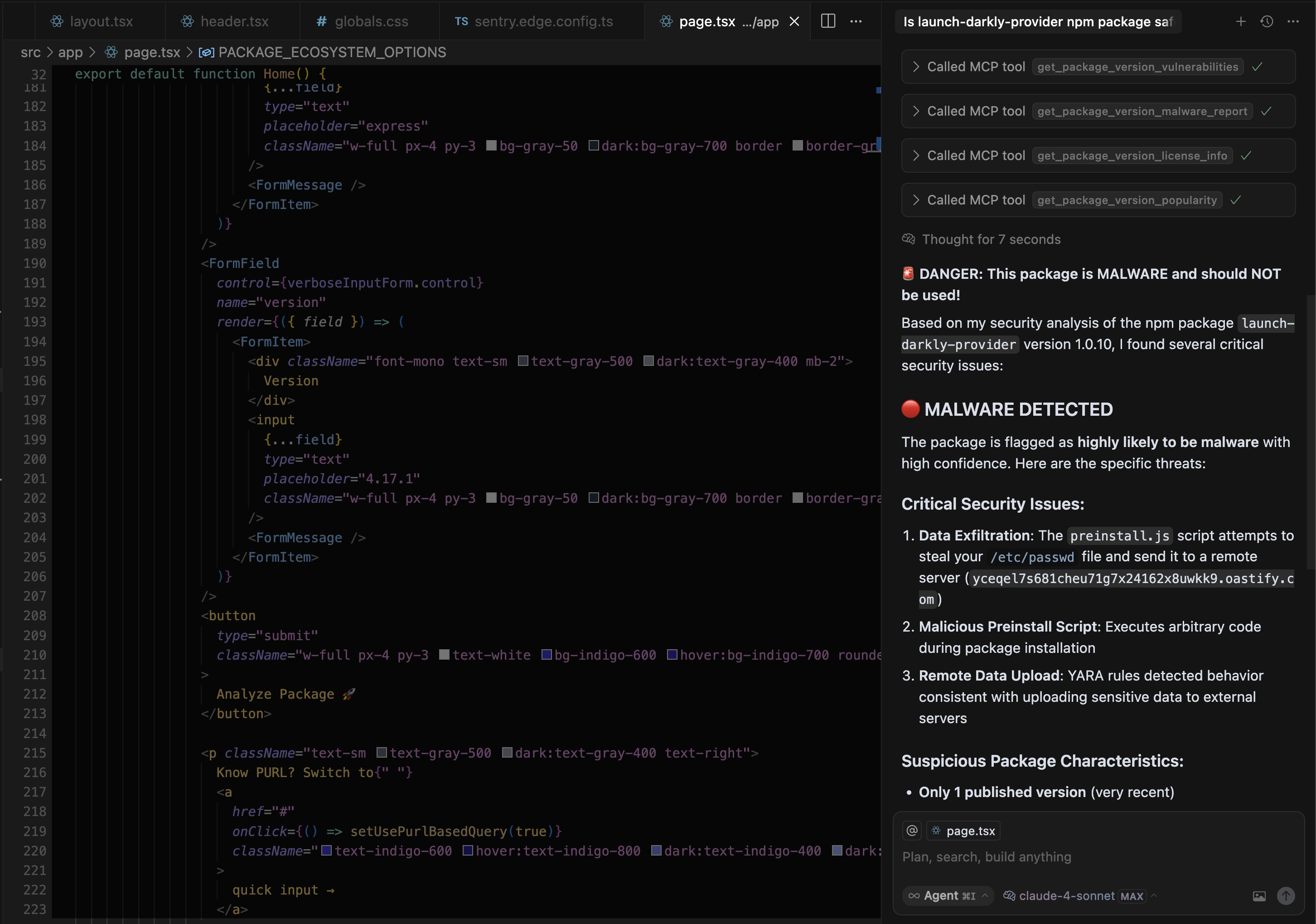
AI Native Software Composition Analysis (SCA)
AI IDE chat interfaces can be used to ask questions about various packages and their vulnerabilities to make sure the code is secure. For example, you can ask: Is npm package launch-darkly-provider safe to use before installation.
Note: launch-darkly-provider is a known malicious package that our systems discovered recently and is not safe to use. For near-real time protection against malicious packages, setup SafeDep vet in your CI/CD pipeline in addition to development environment.
How it works?
The MCP server is built using SafeDep vet as the foundational SCA engine. It is supported by SafeDep Cloud APIs to query for malicious packages that are being continuously updated using SafeDep Malicious Package Scanning service. For community contributions and support, open an issue on SafeDep GitHub or start a GitHub Discussion.
- mcp
- security
- ai-code-generation
- agentic-software-engineering
- slopsquatting
- prompt-injection
- sca
- supply-chain-security
Author
SafeDep Team
safedep.io
Share
The Latest from SafeDep blogs
Follow for the latest updates and insights on open source security & engineering
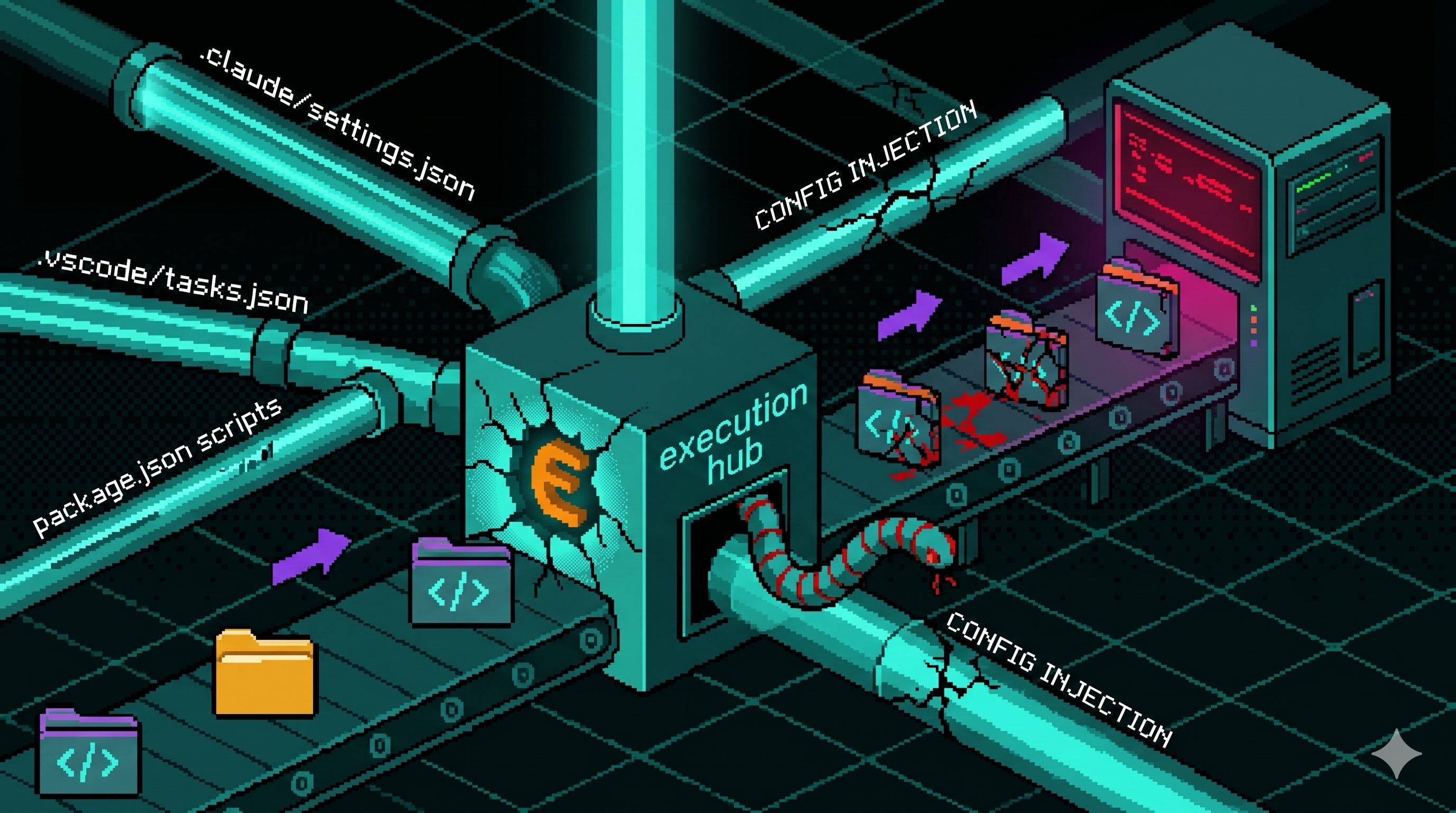
Config Files That Run Code: Supply Chain Security Blindspot
Editor and package-manager config files auto-execute commands when a developer opens a folder or installs dependencies. The Miasma worm wired one dropper into seven of them across Claude Code,...
Axios Typosquats Deliver the Epsilon Stealer
Two axios typosquats on npm, turbo-axios and faster-axios, form a campaign delivering Epsilon Stealer through a four-stage chain. The Electron infostealer grabs browser credentials, crypto wallets,...

Miasma Worm Targets AI Coding Agents via GitHub Repos
A Miasma worm variant injects a 4.3 MB dropper into GitHub repos across multiple maintainers, wiring it to auto-run through Claude Code, Gemini, Cursor, and VS Code config files. No npm package is...
Mini Shai-Hulud "Miasma: The Spreading Blight" Hits @redhat-cloud-services: Multiple Packages at Risk
The attacker compromised the @redhat-cloud-services GitHub Actions OIDC trusted publisher to ship [email protected] with a Mini Shai-Hulud worm. The same publisher controls 32 packages across the...

Ship Code.
Not Malware.
Start free with open source tools on your machine. Scale to a unified platform for your organization.
