Introducing vetpkg.dev - Open Source Component Security Dashboard
Table of Contents
Introducing vetpkg.dev
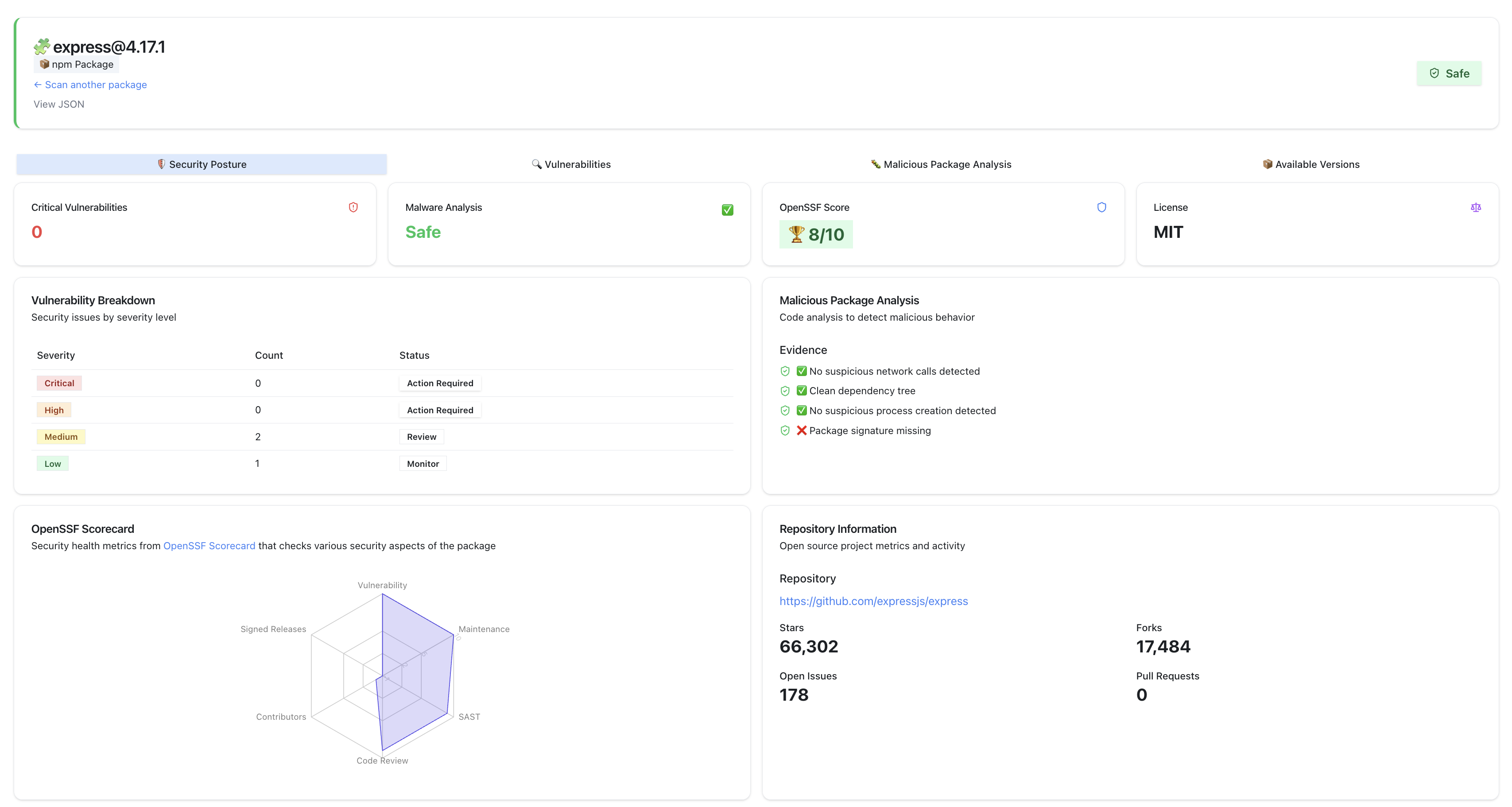
vetpkg.dev is a free service that provides visibility into the security of open source components. It is built using the SafeDep Cloud API to provide an easy to use interface for developers to check the security of their open source dependencies before using them in their projects.
Why did we build vetpkg.dev?
As the developers of vet, we often felt the need for customizing security metadata visualization for open source components. We wanted to mash up public and private data sources to provide easy access to aggregated security data. We expect that this information will help developers and security engineers make better decisions about the open source components before using them in their projects.
Using vetpkg.dev, we want to provide a simple and easy-to-use interface for having a single source of truth for open source component security information including malicious code analysis results.
How to use vetpkg.dev?
Using vetpkg.dev is simple. You can search for an open source component by its ecosystem, name and version. For example, navigate to the following URL
You can also search for specific component by navigating to vetpkg.dev
How does vetpkg.dev work?
vetpkg.dev uses the SafeDep Cloud API to fetch security information about open source components. This includes information about known vulnerabilities, licenses, project metadata, malicious code analysis results and more. It uses SafeDep Insights API to fetch the required information.
Example
The source of screenshot below is available here
- sca
- nextgen-sca
- reachability
- ossrisk
- guide
Author
SafeDep Team
safedep.io
Share
The Latest from SafeDep blogs
Follow for the latest updates and insights on open source security & engineering
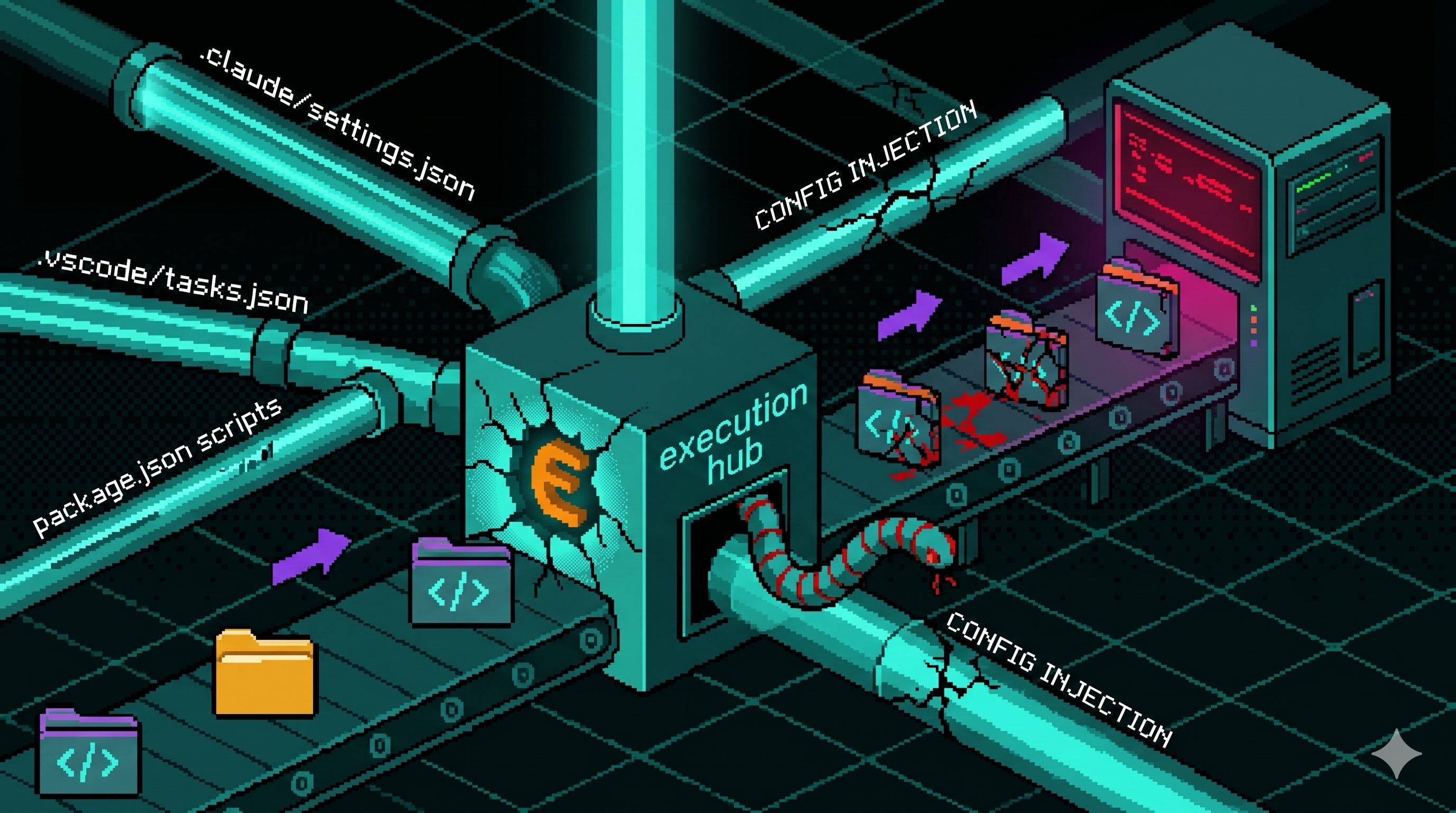
Config Files That Run Code: Supply Chain Security Blindspot
Editor and package-manager config files auto-execute commands when a developer opens a folder or installs dependencies. The Miasma worm wired one dropper into seven of them across Claude Code,...
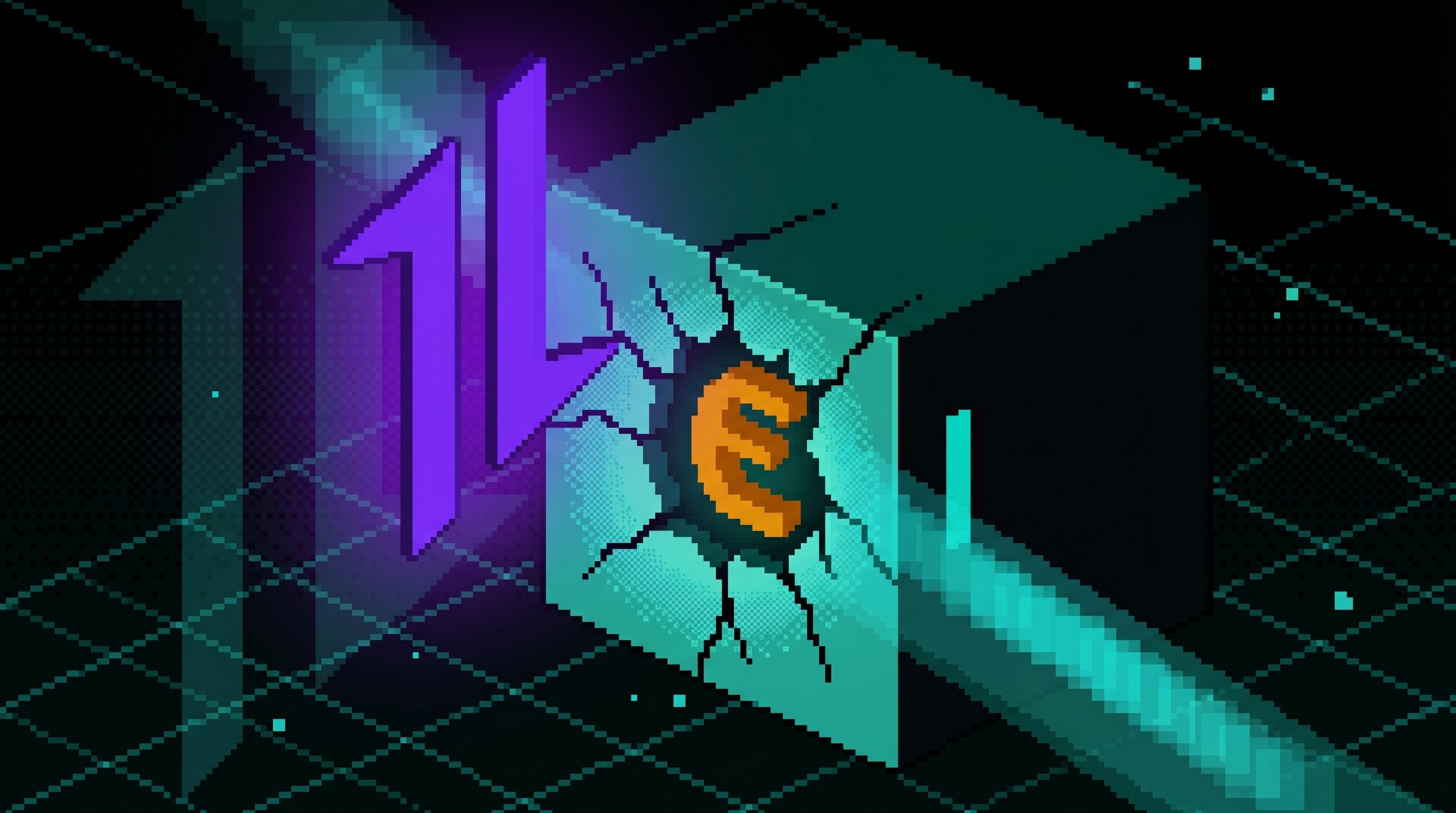
Axios Typosquats Deliver the Epsilon Stealer
Two axios typosquats on npm, turbo-axios and faster-axios, form a campaign delivering Epsilon Stealer through a four-stage chain. The Electron infostealer grabs browser credentials, crypto wallets,...

Miasma Worm Targets AI Coding Agents via GitHub Repos
A Miasma worm variant injects a 4.3 MB dropper into GitHub repos across multiple maintainers, wiring it to auto-run through Claude Code, Gemini, Cursor, and VS Code config files. No npm package is...
Mini Shai-Hulud "Miasma: The Spreading Blight" Hits @redhat-cloud-services: Multiple Packages at Risk
The attacker compromised the @redhat-cloud-services GitHub Actions OIDC trusted publisher to ship [email protected] with a Mini Shai-Hulud worm. The same publisher controls 32 packages across the...

Ship Code.
Not Malware.
Start free with open source tools on your machine. Scale to a unified platform for your organization.
