Typosquatt alert ! Malicious npm Package: nyc-config
Table of Contents
Recently, we discovered a malicious npm package nyc-config in our internal Open Source Software (OSS) package monitoring dashboard. It involved sending user system data to external domains. It is a possible typosquatt attack against the widely adopted @istanbuljs/load-nyc-config, which boasts ~25M weekly downloads.
Discovery and Analysis
Our automated malware analysis flagged the nyc-config package as malicious due to System Information Exfiltration. Upon manual inspection, we observed that the package’s package.json file contained a preinstall script designed to execute the index.js file during installation step itself. This script was crafted to gather sensitive system information such as:
- Hostname
- Operating system details
- Local and public IP addresses
- Username
- Current working directory
The collected data was then exfiltrated to remote servers controlled by the attacker.
You can view the analysis here - https://platform.safedep.io/community/malysis/01JP01T1WQPNGAG516NDS9A6ST
Community Engagement
Recognizing the severity of this threat, we promptly reported our findings to the Open Source Security Foundation (OSSF) - https://github.com/ossf/malicious-packages/pull/839
Conclusion
This incident underscores the critical importance of being cautious when incorporating third-party packages, ensuring they originate from trusted sources. By staying vigilant and fostering collaborative efforts, we can collectively mitigate the risks posed by malicious actors and fortify the security of our development environments.
- npm
- malware
- typosquatting
- open-source security
Author
SafeDep Team
safedep.io
Share
The Latest from SafeDep blogs
Follow for the latest updates and insights on open source security & engineering
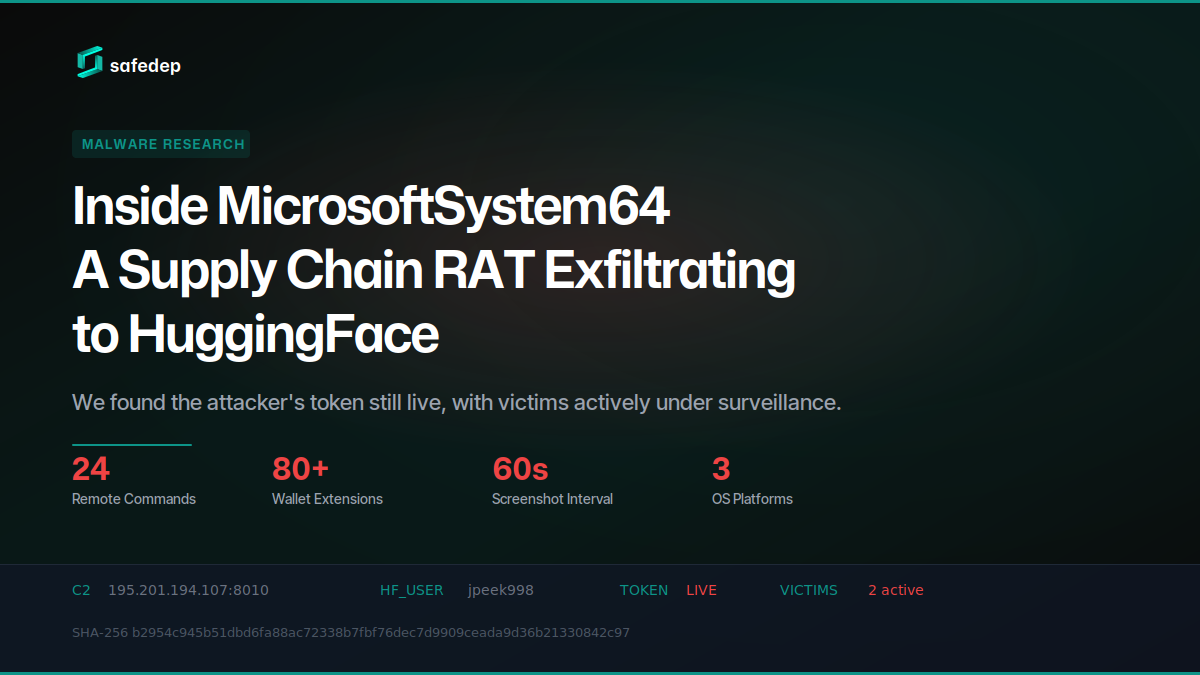
Inside MicrosoftSystem64: A Supply Chain RAT Exfiltrating to HuggingFace
Deep technical analysis of MicrosoftSystem64, an 81 MB Node.js SEA binary deployed via malicious npm packages. This RAT steals browser credentials, 80+ crypto wallet extensions, Telegram sessions,...

141 npm Packages Abuse Registry as Adware Hosting
npm account terminal3airport published 141 packages containing a web proxy unblocker disguised as tutoring websites. The packages load popunder ads, external monetization scripts, and Google...

179 npm Packages Target Cloud and Finance via oob.moika.tech
Two npm accounts published 164 malicious packages at version 99.99.99 targeting a cloud platform and a financial institution. Both campaigns share identical payload code, the same C2 endpoint, and...
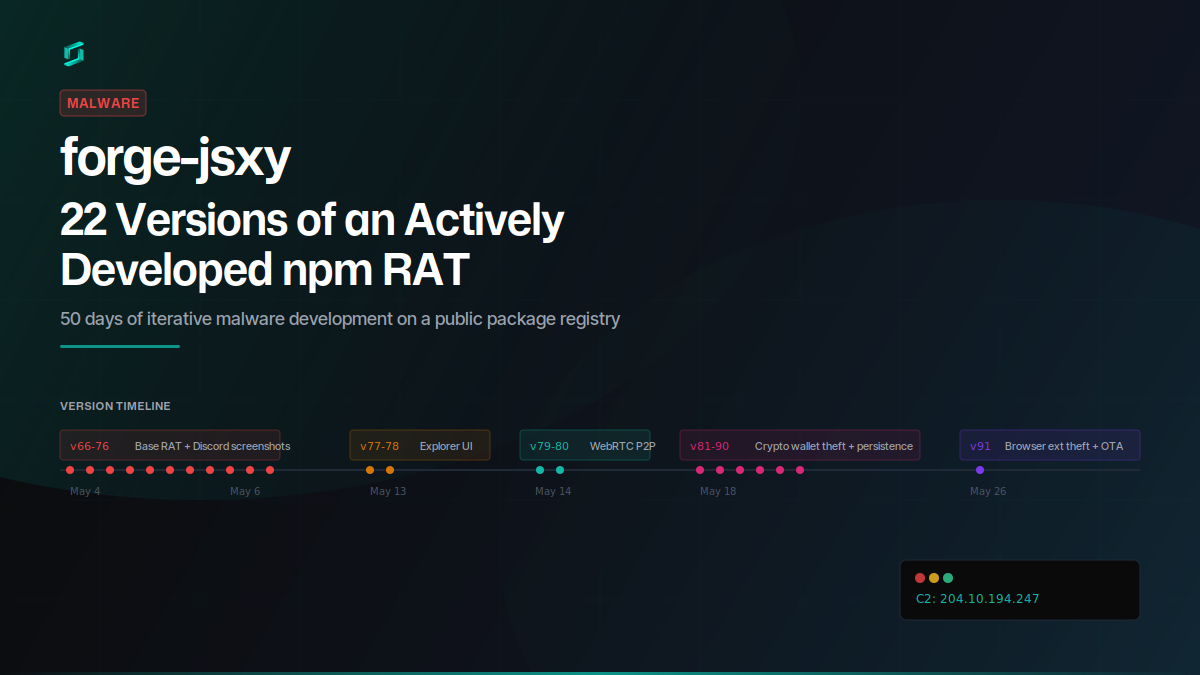
forge-jsxy: 22 Versions of an Actively Developed npm RAT
forge-jsxy picked up where the taken-down forge-jsx left off, publishing 22 versions over 22 days. Each release added new capabilities: crypto wallet scanning, Chromium extension theft, WebRTC data...

Ship Code.
Not Malware.
Start free with open source tools on your machine. Scale to a unified platform for your organization.
