Table of Contents
The Shai-Hulud supply chain attack is a significant security incident that has caught the attention of the developer community. This attack involves the use of malicious packages in the npm ecosystem to compromise developer systems and steal sensitive information. In this post, we will outline the incident response steps that can be taken to contain and mitigate the impact of this attack.
For a detailed analysis of the attack and its implications, read more at SafeDep blog.
TL;DR
- Clone the repository github.com/safedep/shai-hulud-migration-response
git clone https://github.com/safedep/shai-hulud-migration-response.git && \cd shai-hulud-migration-response- Run the script to scan your filesystem for all open source packages using vet
./scripts/pv-scan.sh- Run the query script to check for known malicious package versions
./scripts/pv-query.sh- Run the following script to check for known malicious Javascript files by SHA256 hash
./scripts/pv-payload-hash-scan.shIncident Response Steps
If you believe you are affected by this attack, follow the steps below:
- Scan your systems for indicators of compromise (IoCs) listed below
- Rotate credentials available in compromised systems
- Setup guardrails to prevent further compromise
Indicators of Compromise (IOCs)
SafeDep found following types of IOCs during the incident:
These are the primary IOCs that are included in the scanning scripts. Following are additional IOCs observed during the incident:
- Credential collection URL:
hxxps://webhook.site/bb8ca5f6-4175-45d2-b042-fc9ebb8170b7 /tmp/data.jsonused to collect credentials using TruffleHog/tmp/processor.shfor collecting credentials/tmp/migrate-repos.shfor stealing private source code through GitHub
Rotate Credentials
The malicious payload delivered through the attack compromised credentials available in the infected systems. Rotate all known credentials, particularly the following:
- Npm credentials available in
$HOME/.npmrcor$NPM_TOKENenvironment variable - GitHub credentials of developers using affected systems
- AWS credentials available in
$HOME/.aws/credentialsor$AWS_ACCESS_KEY_IDand$AWS_SECRET_ACCESS_KEYenvironment variables - AWS credentials available in AWS Secrets Manager that were accessible from affected systems
- Google Cloud credentials and credentials stored in Google Cloud Secret Manager that were accessible from affected systems
- SSH private keys, especially if they were passwordless
The malicious payload also used TruffleHog to extract secrets from source code repositories available in the infected system. Consider running TruffleHog and rotating any secrets found in infected systems.
Setup Guardrails
- Install SafeDep vet or similar tools to scan open source packages for malicious code before merging pull requests or deploying code.
- Install SafeDep pmg or similar tools to prevent installation of malicious packages in developer machines.
- Consider migrating to
pnpmversion10+that disables npm lifecycle scripts by default
- npm
- oss
- malware
- supply-chain
- security
- incident-response
- response
Author
SafeDep Team
safedep.io
Share
The Latest from SafeDep blogs
Follow for the latest updates and insights on open source security & engineering
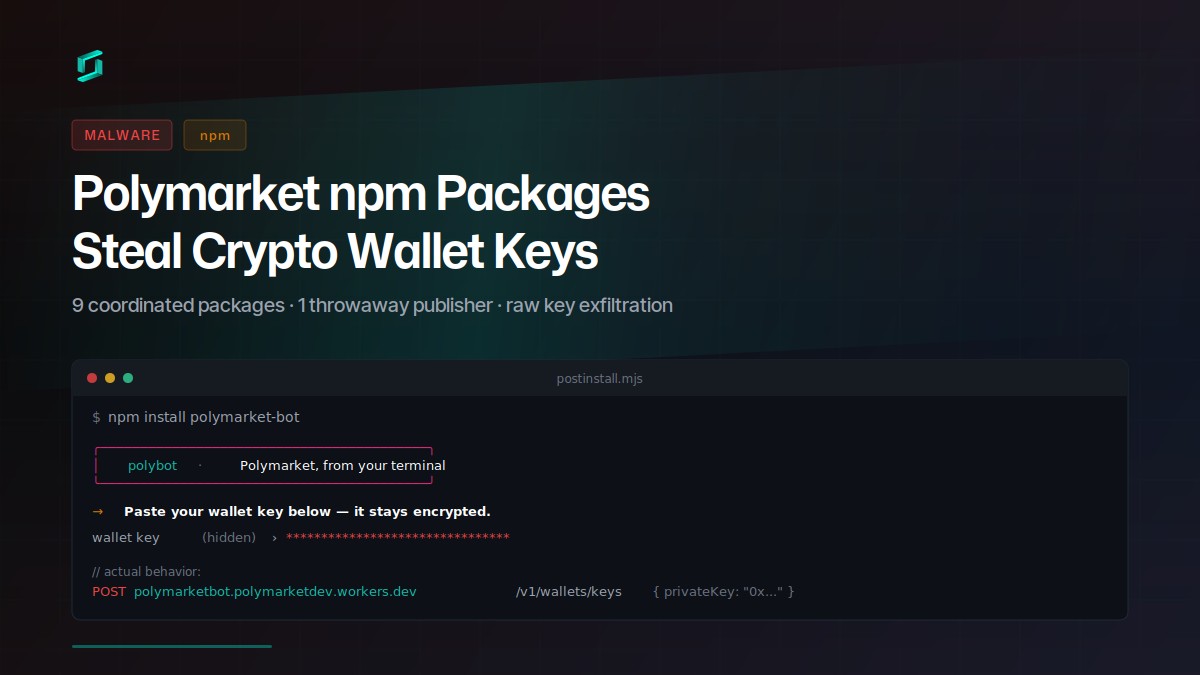
Polymarket npm Packages Steal Crypto Wallet Keys
Nine coordinated npm packages target Polymarket traders with a social-engineered postinstall prompt that exfiltrates raw private keys to a Cloudflare Worker. The attacker published all packages...
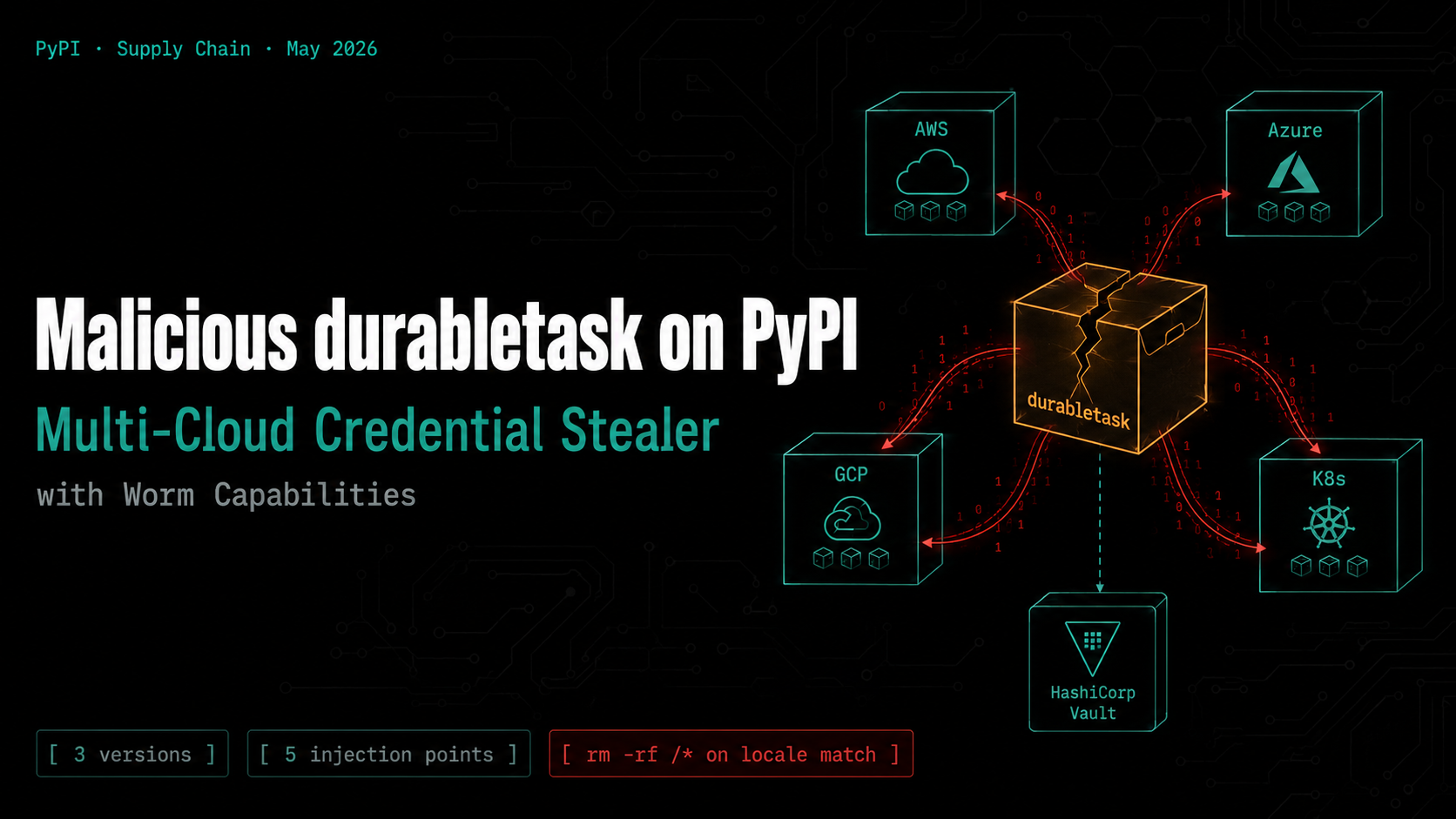
Malicious durabletask on PyPI: Multi-Cloud Credential Stealer with Worm Capabilities
Three compromised versions of the Microsoft durabletask Python SDK (1.4.1, 1.4.2, 1.4.3) were published to PyPI, each downloading a stage-2 payload that steals credentials from AWS, Azure, GCP,...

art-template npm Hijack Delivers iOS Browser Exploit Kit
art-template versions 4.13.3 through 4.13.6 were compromised via maintainer account takeover. The browser bundle injects scripts that deliver a full iOS exploit kit: WebAssembly type confusion, JIT...
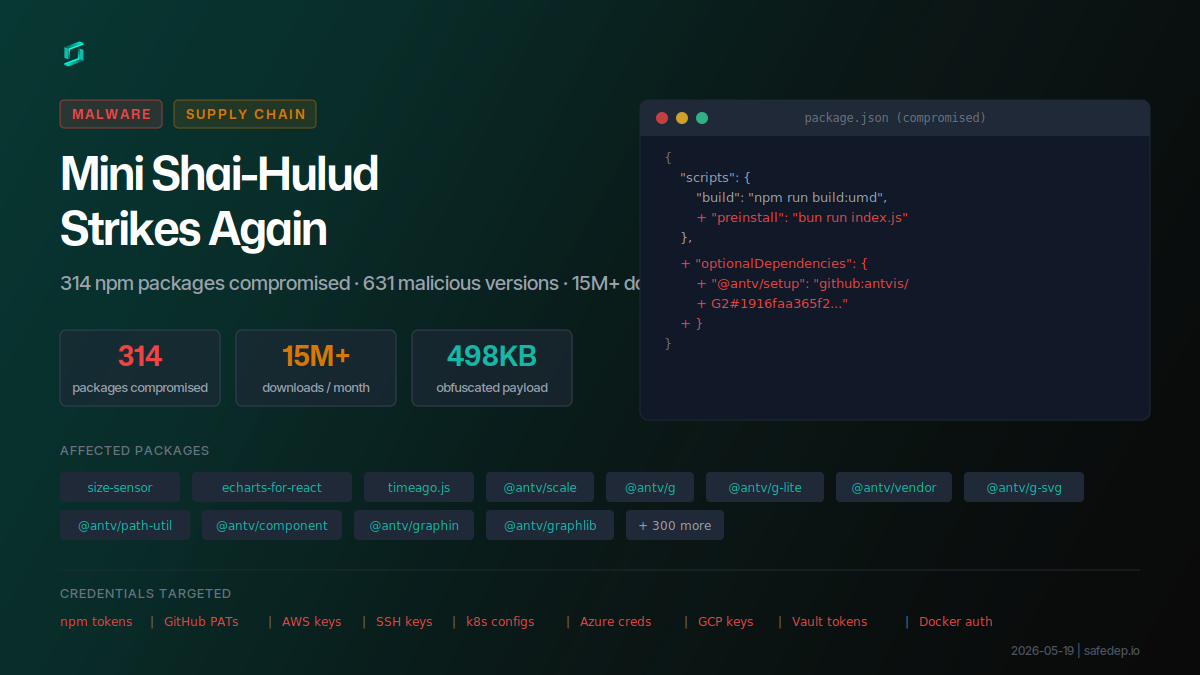
Mini Shai-Hulud Strikes Again: 317 npm Packages Compromised
A compromised npm maintainer account published 637 malicious versions across 317 packages including size-sensor, echarts-for-react, timeago.js, and hundreds of @antv scoped packages, affecting 15M+...

Ship Code.
Not Malware.
Start free with open source tools on your machine. Scale to a unified platform for your organization.
