Endpoint Protection for Developer Machines
Table of Contents
PMG is an open source package guard that intercepts every npm install or pip install before any post-install script can execute. For teams, syncing pmg with SafeDep Cloud gives you a per-endpoint audit trail of every install, block, and override across your entire developer fleet.
The gap in your current security posture
Most teams have some form of dependency scanning. A CI job checks lockfiles. A CVE feed alerts when a known-bad package shows up in a manifest. If the security stack is mature, an SCA tool runs on pull requests.
None of it runs before npm install completes.
Malicious packages execute in post-install scripts. The payload runs the moment the package lands on disk, well before your next commit or PR. On a developer laptop. In a CI runner. In an AI coding agent’s sandboxed environment. By the time a pipeline scanner surfaces the alert, the credentials are gone, the reverse shell is open, or the backdoor is installed.
The eslint-config-prettier supply chain attack followed this exact pattern. The Strapi campaign did too. The endpoint is where the attack actually lands, and most teams have nothing running there.
PMG: one alias between you and the next supply chain attack
pmg wraps your package manager. Set one alias and every install command goes through threat intelligence first.
# Install via Homebrew (macOS)brew install safedep/tap/pmg
# Or download from https://github.com/safedep/pmg/releases
# One-time setup: registers pmg aliases in your shellpmg setup installAfter that, npm, pip, and cargo commands route through pmg. No tokens required. No account. No configuration.
pmg npm install express# [info] checking threat intelligence...# ✓ [email protected] — allowedWhen it catches something:
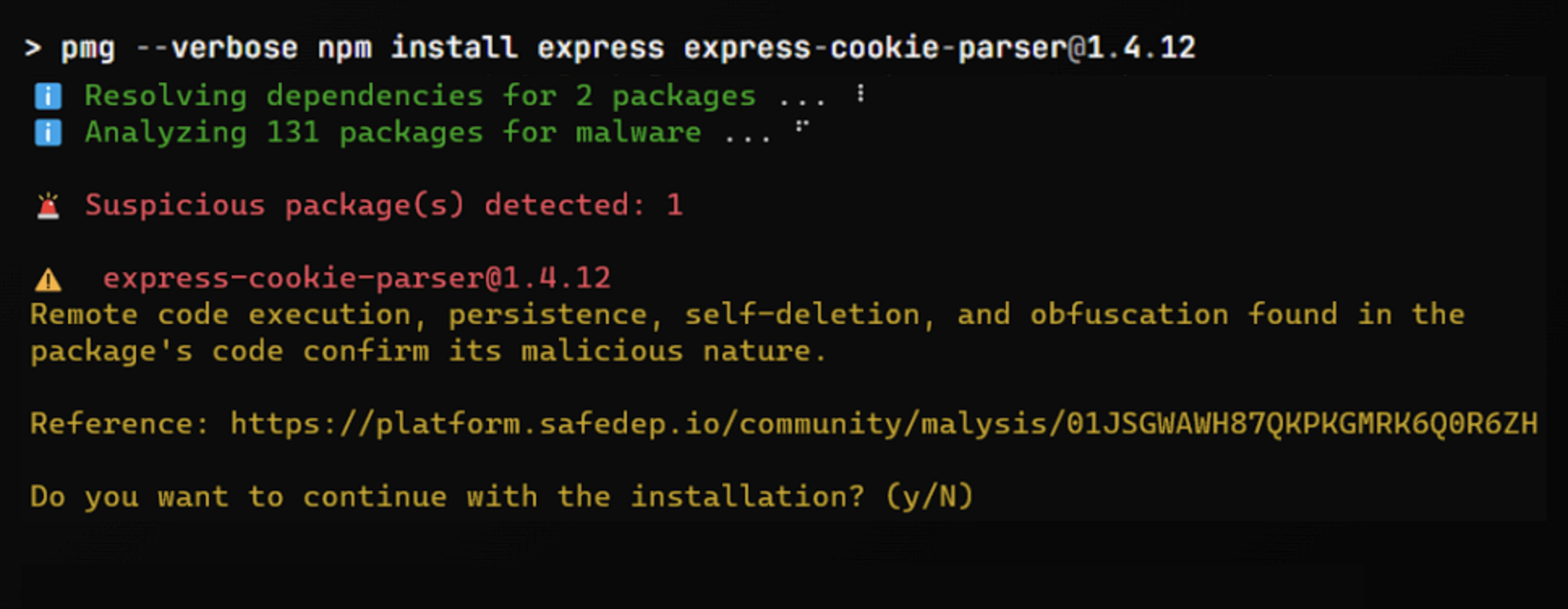
The check happens before any post-install script fires. If the package carries a human-verified malicious verdict in SafeDep’s threat intelligence, the install aborts. The payload never runs.
pmg also supports dependency cooldown: a configurable window (say, five days) that gates installs on publication age. Packages published within the cooldown period are blocked or fall back to the newest eligible version. This catches supply chain attacks that exploit the window between publication and detection, before any threat intelligence verdict exists.
PMG is free and entirely open source: github.com/safedep/pmg.
Scaling to your team: cloud sync
PMG on a single laptop protects one developer. For org-wide coverage, you need visibility across every endpoint in your fleet.
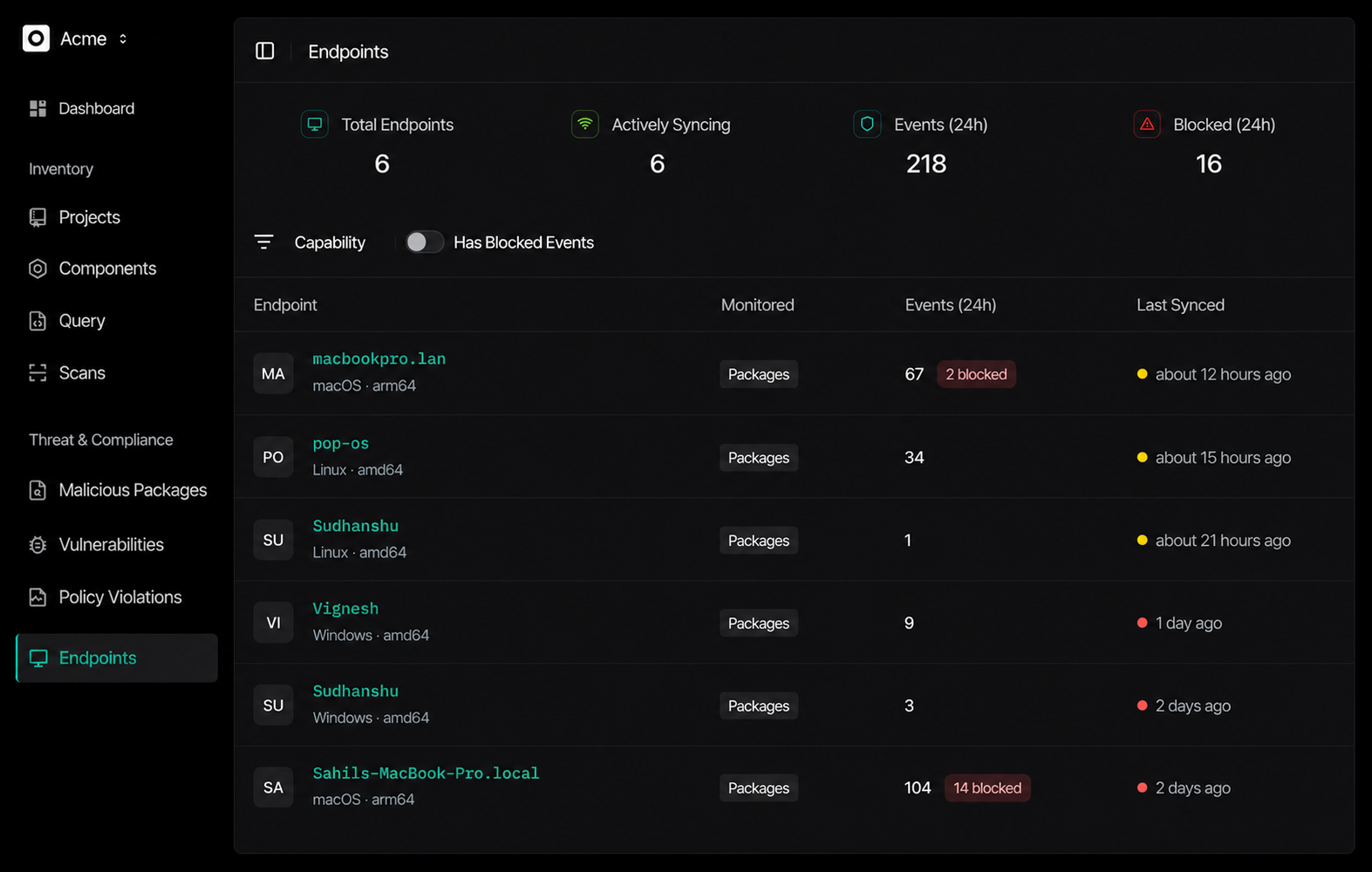
pmg cloud sync connects each endpoint to your SafeDep Cloud tenant. After authenticating, every package event streams to the central dashboard at app.safedep.io/endpoints.
# Authenticate once per machinepmg cloud login# ? tenant id: acme# ? domain: acme.safedep.io# ✓ logged in
# Sync package events to SafeDep Cloudpmg cloud sync# ↑ pushing 142 package events# ↑ pushing 28 sessions# ✓ synced to app.safedep.ioThe Endpoints dashboard shows every registered machine, its last sync time, and aggregate event counts for the past 24 hours: total events, blocked installs, active endpoints.
For CI pipelines, add pmg cloud sync as a post-step after your install phase. Every build’s package activity becomes part of the audit trail.
Package events: the audit trail
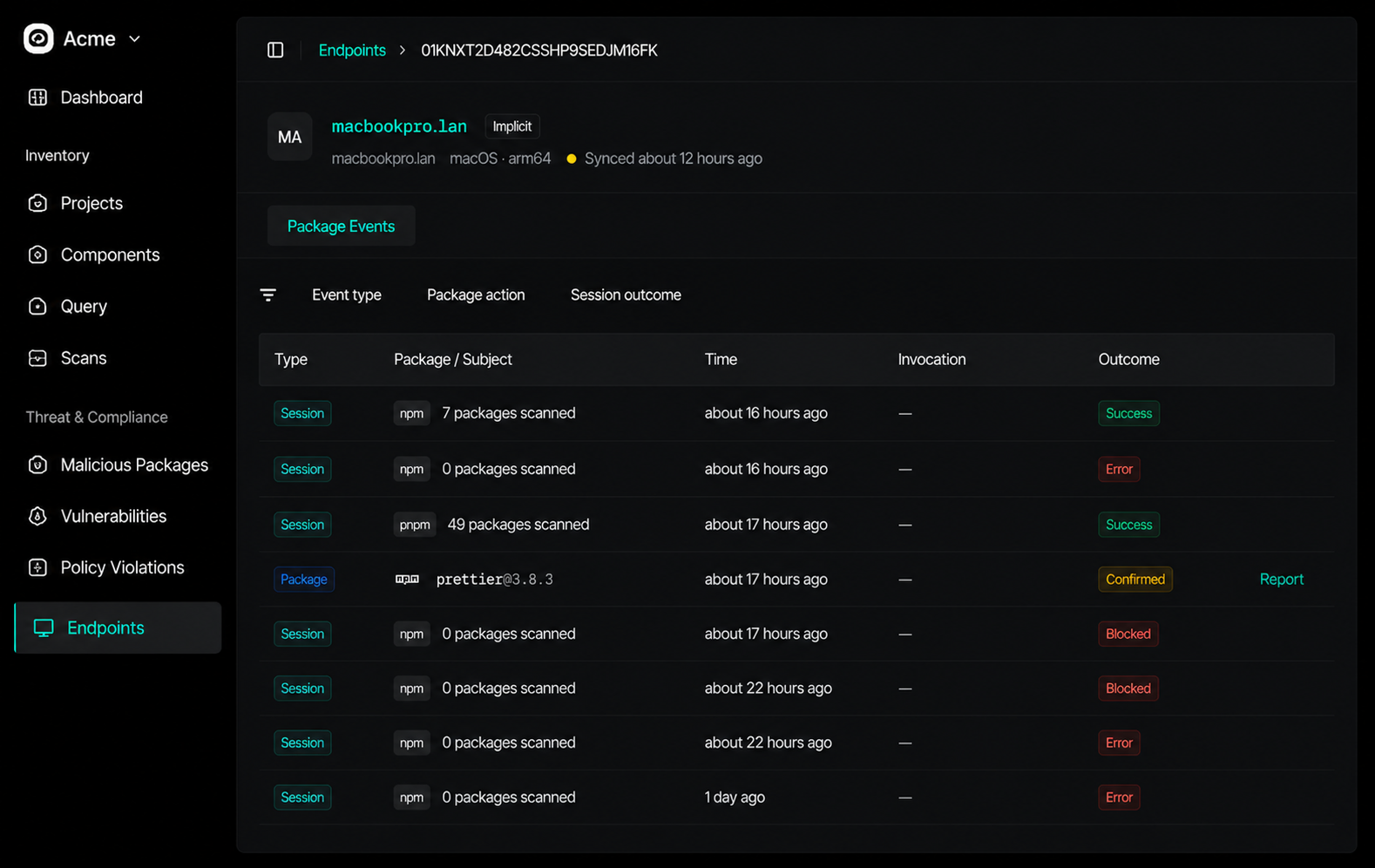
Once endpoints sync, you work with package events rather than aggregate counts. Each event carries the ecosystem (npm, PyPI, crates.io), the package name and version, the action (install, remove, update), and the outcome.
The four outcomes are what your security team actually needs:
allowed— install completed cleanlyblocked— stopped by threat intelligence or cooldownoverride— developer force-installed despite a blockbypassed—pmgwas skipped via flag
override and bypassed are the operationally interesting ones. They show which developer pushed through a block, against which package, and when. Without this signal, you have no visibility into how often your enforcement is being worked around.
The per-endpoint view shows the full package guard stream for any machine, drill-down to individual sessions:
Inventory events: what’s already on the machine
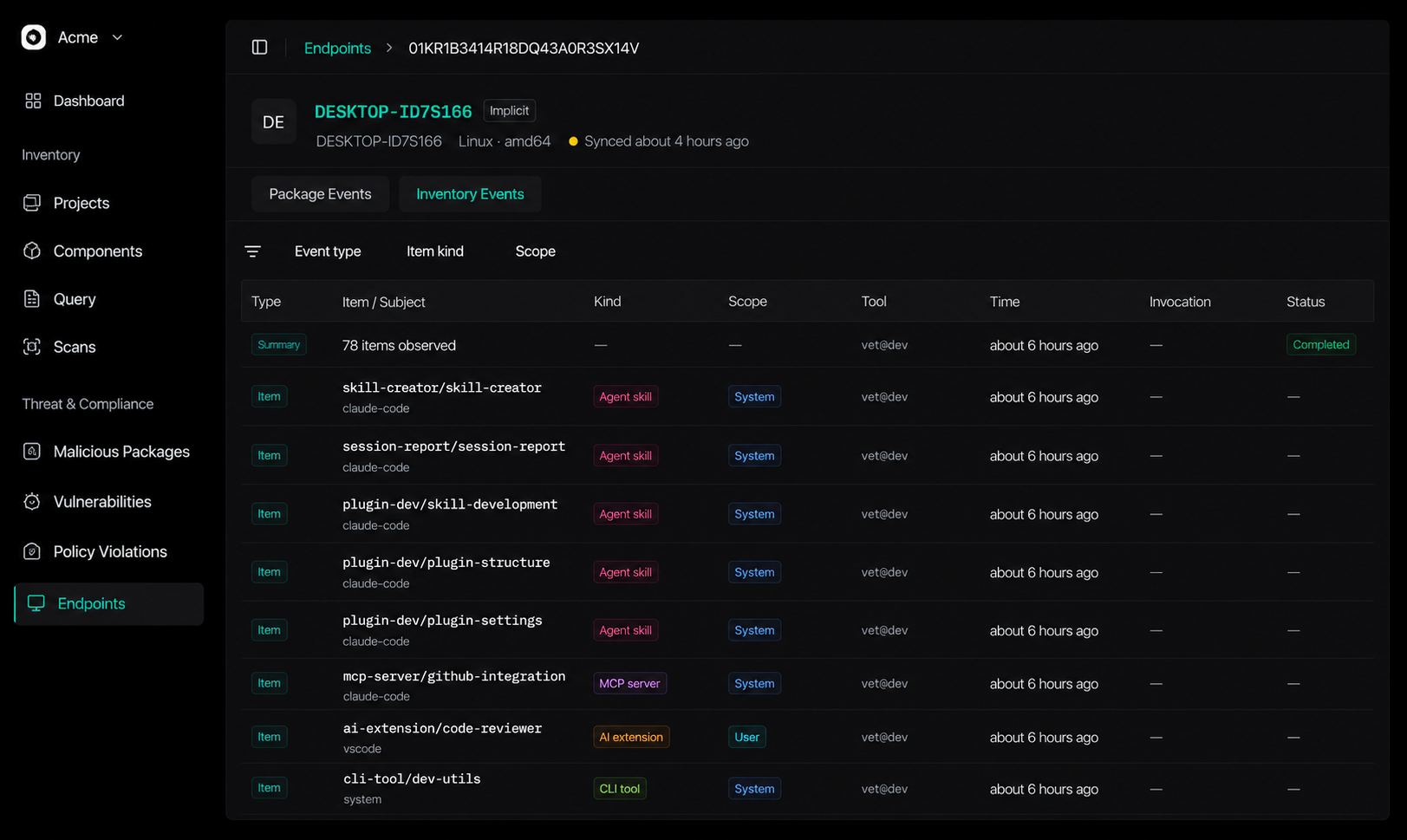
Package events cover what developers install going forward. A separate question is what’s already installed on each endpoint: which AI tools, MCP servers, CLI tools, and IDE extensions are running system-wide.
vet endpoint scan handles this. It inventories the tooling on an endpoint and reports the results back to SafeDep Cloud, where they appear under the Inventory tab.
# Configure authenticationvet auth configure --tenant <your-domain.safedep.io>vet auth verify
# Scan the endpoint (system-wide)vet endpoint scan --scope system
# Or limit to the current project directoryvet endpoint scan --scope projectThis gives security teams a fleet-wide view of the tool ecosystem, not just what was installed today. Combined with package events, it answers both “what is running on this machine” and “what was installed and when.”
Quick start
For individual developers:
brew install safedep/tap/pmgpmg setup install# Every package install is now checked. Done.For team-wide visibility:
pmg cloud login # once per machinepmg cloud sync # after any install session, or on a scheduleFor endpoint inventory:
brew install safedep/tap/vetvet auth configure --tenant <your-domain.safedep.io>vet endpoint scan --scope systemFull setup documentation covers CI integration, policy configuration, and multi-tenant deployment:
- Package guard setup: docs.safedep.io/cloud/endpoint-hub/package-guard
- Endpoint Hub (including vet inventory sync): docs.safedep.io/cloud/endpoint-hub
What changes with endpoint visibility
Repository scanning and endpoint protection cover different moments. Repo scanning finds what’s in your committed code. Endpoint protection stops what tries to run before any commit exists.
The attacks that defined recent supply chain threat reports had one thing in common: the payload executed before any public advisory, CVE, or pipeline alert existed. Threat intelligence only matters if something at the endpoint acts on it in time.
pmg provides that enforcement. The cloud sync makes it observable at scale.
- pmg
- endpoint-protection
- supply-chain
- npm
- developer-security
Author
SafeDep Team
safedep.io
Share
The Latest from SafeDep blogs
Follow for the latest updates and insights on open source security & engineering
Axios Typosquats Deliver the Epsilon Stealer
Two axios typosquats on npm, turbo-axios and faster-axios, form a campaign delivering Epsilon Stealer through a four-stage chain. The Electron infostealer grabs browser credentials, crypto wallets,...
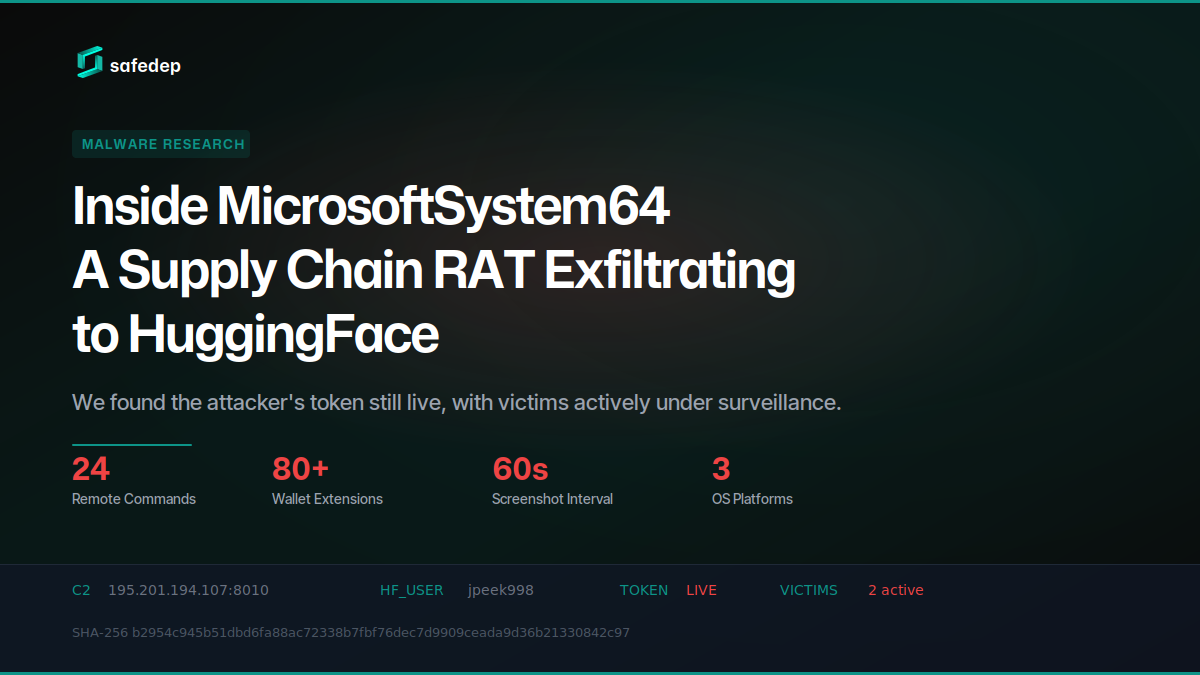
Inside MicrosoftSystem64: A Supply Chain RAT Exfiltrating to HuggingFace
Deep technical analysis of MicrosoftSystem64, an 81 MB Node.js SEA binary deployed via malicious npm packages. This RAT steals browser credentials, 80+ crypto wallet extensions, Telegram sessions,...
Mini Shai-Hulud "Miasma: The Spreading Blight" Hits @redhat-cloud-services: Multiple Packages at Risk
The attacker compromised the @redhat-cloud-services GitHub Actions OIDC trusted publisher to ship [email protected] with a Mini Shai-Hulud worm. The same publisher controls 32 packages across the...

183 npm Packages Target Cloud and Finance via oob.moika.tech
Two npm accounts published 164 malicious packages at version 99.99.99 targeting a cloud platform and a financial institution. Both campaigns share identical payload code, the same C2 endpoint, and...

Ship Code.
Not Malware.
Start free with open source tools on your machine. Scale to a unified platform for your organization.
