exiouss: Cookie Stealer Bundled in npm Exam Cheat
Table of Contents
TL;DR
[email protected] published to npm on 2026-05-01 from the loltestpad account, the same account behind ixpresso-core (a full Windows RAT), godsplan, and eyevox in April before npm removed them within 48 hours. exiouss is godsplan rebuilt under a new name with the same fake description and the same internal project name. It adds one capability the April packages lacked: bin/chrome_cookies.ps1, a complete PowerShell script that decrypts and exfiltrates Chrome, Edge, and Brave session cookies for openai.com and chatgpt.com. The script is not yet wired into the main flow, but it is present and functional.
Impact:
- The package bundles a complete ChatGPT and OpenAI session cookie stealer targeting Chrome, Edge, and Brave via Windows DPAPI and AES-256-GCM decryption
- The attacker targets students who install this to cheat on proctored exams, an audience likely to hold active ChatGPT Plus subscriptions
- The
loltestpadaccount published four packages across two campaigns, iterating from a Windows RAT to a cheating tool with a dormant credential stealer
Indicators of Compromise (IoC):
| Indicator | Value |
|---|---|
| Package | [email protected] |
| npm maintainer | loltestpad |
| Maintainer email | [email protected] |
| Stealth process | SearchApp.exe |
| Persistence path | %LOCALAPPDATA%\Microsoft\Windows\Diagnostics\ |
| Boot log | %LOCALAPPDATA%\Microsoft\Windows\Diagnostics\boot.log |
| Kill switch file | %LOCALAPPDATA%\Microsoft\Windows\Diagnostics\.kill_watchdog |
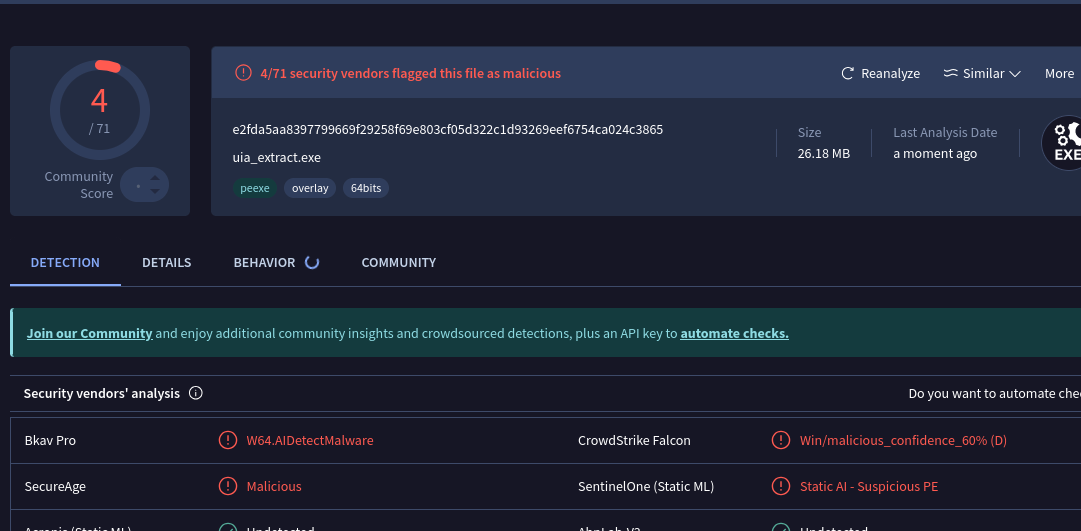
uia_extract.exe SHA256 | e2fda5aa8397799669f29258f69e803cf05d322c1d93269eef6754ca024c3865 |
uia_extract.exe VirusTotal | 4/71 — Bkav, CrowdStrike, SecureAge, SentinelOne (all ML-based) |
| Groq API keys | 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 (+ 3 more in config.json) |
The loltestpad Campaign
The loltestpad account appeared on 2026-04-14 with a throwaway email on opemails.com, a disposable mail service. Within 48 hours, it published three packages:
| Package | Published | Real function | Cover description |
|---|---|---|---|
ixpresso-core | 2026-04-14 | Windows RAT (Veltrix) | “Personal AI System Agent — Control your device via WhatsApp” |
godsplan | 2026-04-14 | AI exam cheating tool | ”High-performance DOM utility and diagnostic bridge” |
eyevox | 2026-04-15 | Lightweight exam cheating variant | ”Professional Stealth AI Assistant with Multi-Snapshot Reasoning” |
npm removed all three within 48 hours. SafeDep’s analysis of ixpresso-core is covered separately — it deployed a full Windows RAT with browser credential harvesting, Discord token theft, Telegram session exfiltration, and remote desktop over a Cloudflare tunnel.
exiouss appeared on npm on 2026-05-01, 16 days after the April takedown. The cover description matches godsplan’s word-for-word: “High-performance DOM utility and diagnostic bridge for modern web applications.” main.js names the project Project Phantom-Batch, identical to the April version. The internal version jumped to v12.0, indicating development continued after the takedown.
$ curl -s "https://registry.npmjs.org/exiouss" | jq '{maintainers, versions: (.versions | keys)}'{ "versions": ["1.0.4"]}Six earlier versions (1.0.0 through 1.0.10) appear in the registry time object. All six were pulled before this analysis, leaving 1.0.4 active.
Both campaigns follow the same pattern: throwaway account, disposable email, fake developer-tool description, Windows-only payload, npm as distribution infrastructure. The attacker uses npm as a hosting and credibility layer, not as a poisoning vector. “Just npm install -g exiouss” reads more legitimate than a Discord download link.
The Bundled Credential Stealer
bin/chrome_cookies.ps1 is new to this version. The April packages did not include it.
The script implements Chrome DPAPI + AES-256-GCM cookie decryption. It reads the encrypted master key from each browser’s Local State file, decrypts it with ProtectedData.Unprotect, then iterates cookies for openai.com, chatgpt.com, auth.openai.com, and auth0.openai.com across Chrome, Edge, and Brave, covering multiple browser profiles each.
$Domains = @(".openai.com", ".chatgpt.com", "chatgpt.com", "openai.com", "chat.openai.com", "auth0.openai.com", "auth.openai.com")...$encKeyBytes = $encKeyBytes[5..($encKeyBytes.Length - 1)]$decryptedKey = [Security.Cryptography.ProtectedData]::Unprotect( $encKeyBytes, $null, [Security.Cryptography.DataProtectionScope]::CurrentUser)main.js never calls this script. It ships in the tarball for the attacker to run separately, or to wire into a future version. A valid auth.openai.com session cookie gives full ChatGPT account access without a password — the attacker can change the email, lock the original owner out, and absorb the subscription.
The victim pool makes this worthwhile. Students running exam cheating tools on Windows have ChatGPT accounts, many with active Plus subscriptions they use for coursework. The exam cheat gets the attacker onto those machines. The cookie stealer monetises that access.
How Students Get Infected
exiouss deploys a persistent Electron overlay when run: a transparent always-on-top window invisible to proctoring screenshot capture via WDA_EXCLUDEFROMCAPTURE, hidden from Alt-Tab and the taskbar. The student captures the exam question using Windows UI Automation text extraction or a GDI screenshot, sends it to Groq’s LLM API via four hardcoded API keys in config.json, and the answer renders in the overlay. The package handles Safe Exam Browser by detecting its isolated secure desktop and spawning a child Electron process onto it via CreateProcessW.
The uia_extract.exe binary scores 4/71 on VirusTotal, all ML-based. Windows Defender shows clean. Most exam machines run no AV that catches this. The cheating tool works well enough to spread through student communities, which puts the credential stealer on a growing number of machines without additional distribution cost.
Conclusion
The loltestpad attacker returned 16 days after the April takedown with the same account, the same description, and the same codebase. The addition is chrome_cookies.ps1: a ChatGPT session stealer, present and functional, not yet active.
The threat model is social engineering, not a poisoned lockfile. Students install this willingly. The cookie stealer sits dormant until the attacker activates it, either wired into a future version or triggered through the watchdog process that stays resident after the terminal closes.
Treat any system that ran exiouss as potentially compromised. Check %LOCALAPPDATA%\Microsoft\Windows\Diagnostics\ for SearchApp.exe and boot.log. Rotate credentials stored in Chrome, Edge, and Brave. Revoke any OpenAI API keys stored in the browser.
Run vet against your lockfiles to flag packages from recently created accounts before install.
Related:
- ixpresso-core: Windows RAT Disguised as a WhatsApp Agent — the RAT from the same
loltestpadcampaign - forge-jsx npm Package: Purpose-Built Multi-Platform RAT — another Electron-based Windows malware pattern
- Malicious dom-utils-lite npm SSH Backdoor via Supabase — fake DOM utility, real backdoor
- malware
- npm
- supply-chain
- credential-theft
- campaign
Author
Kunal Singh
safedep.io
Share
The Latest from SafeDep blogs
Follow for the latest updates and insights on open source security & engineering

PyTorch Lightning Compromised: Shai-Hulud Worm Reaches PyPI
PyPI yanked PyTorch Lightning versions 2.6.2 and 2.6.3 after both embedded a two-stage credential-stealing payload. Any import of the library spawns an 11MB obfuscated JavaScript worm identical to...
Malicious redeem-onchain-sdk npm Targets Crypto Wallets
redeem-onchain-sdk impersonates a Polymarket helper SDK and exfiltrates SSH keys, AWS credentials, npm tokens, Docker configs, Chrome saved logins, and a month of local git history to an AWS-hosted...

Mini Shai Hulud and SAP Compromise
Four SAP npm packages published on April 29, 2026 contain a two-stage credential-stealing payload targeting GitHub tokens, AWS keys, and CI/CD pipelines. The packages share SAP-affiliated...
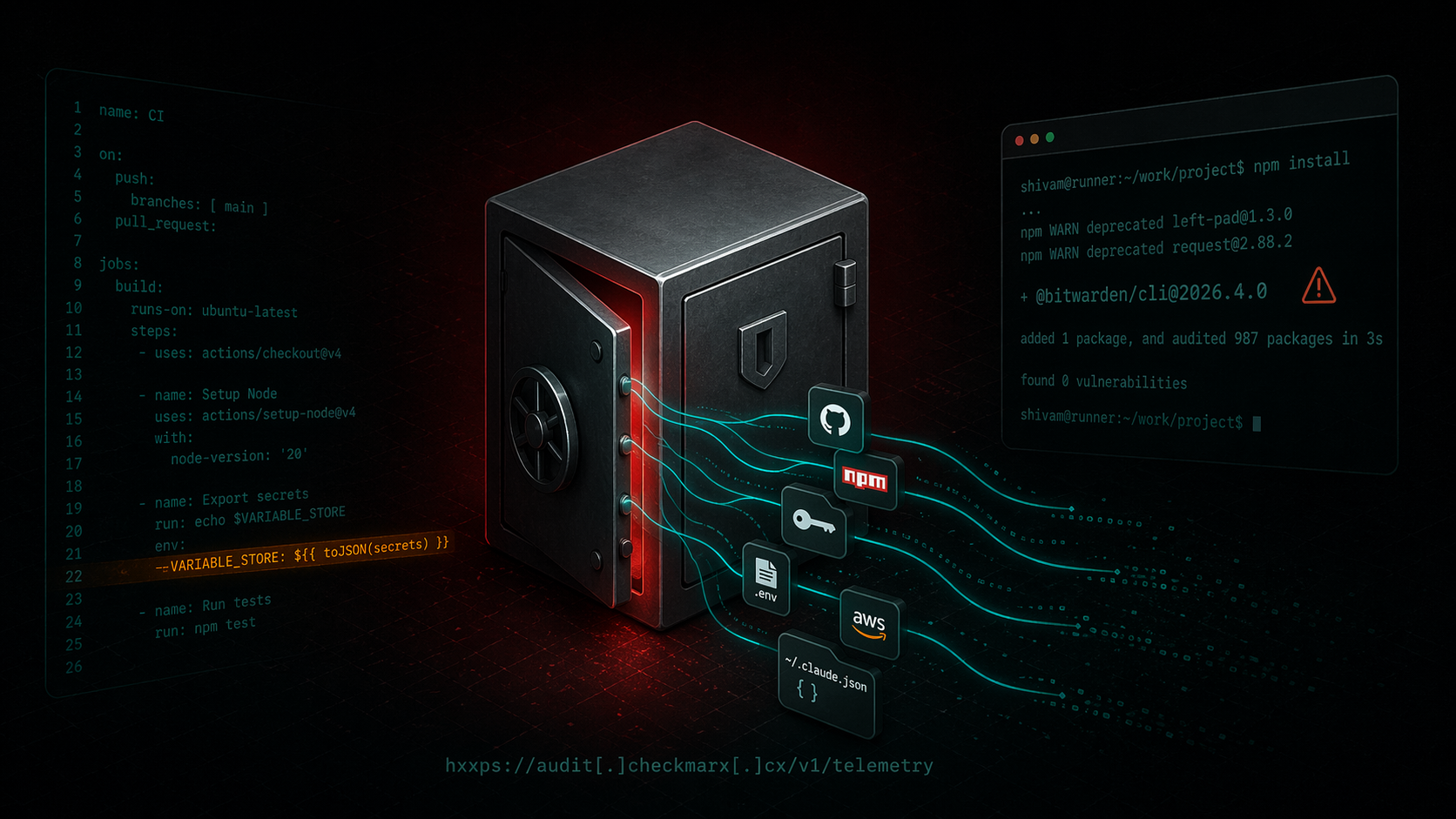
Bitwarden CLI Supply Chain Compromise
A technical writeup of the malicious `@bitwarden/[email protected]` release linked to the Checkmarx campaign. Covers the poisoned publish path, loader changes, credential theft, GitHub abuse, and...

Ship Code.
Not Malware.
Start free with open source tools on your machine. Scale to a unified platform for your organization.

