Why We Built a Hosted MCP Server to Stop Malicious Packages for AI Agents
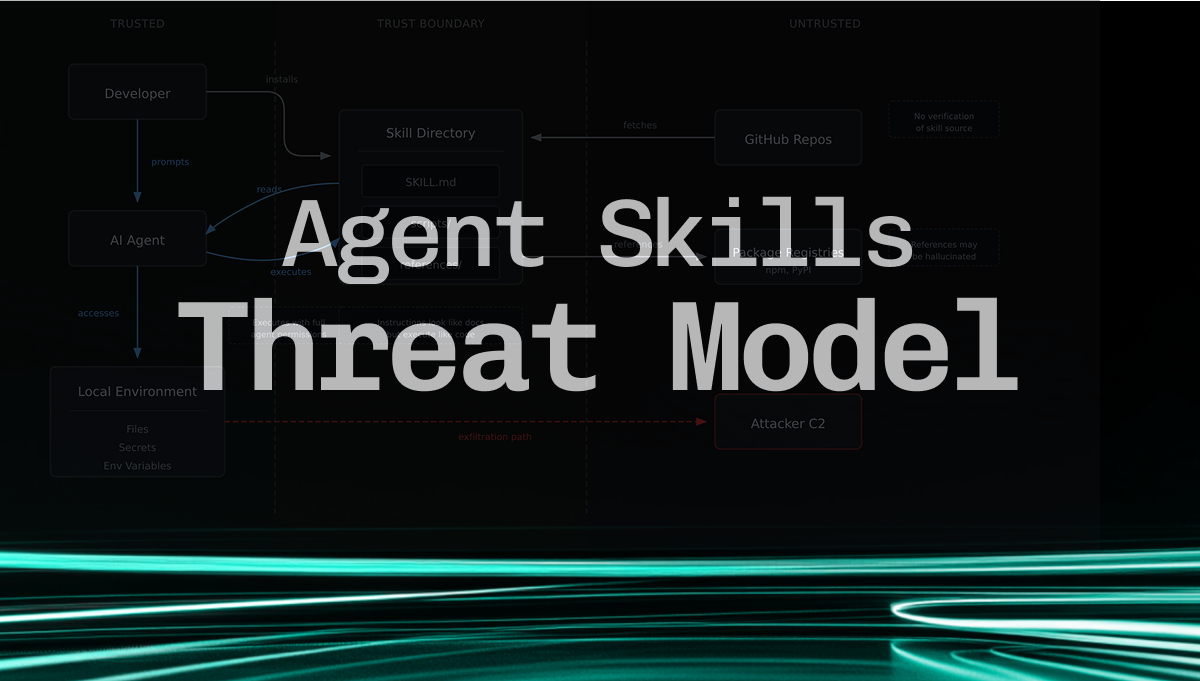
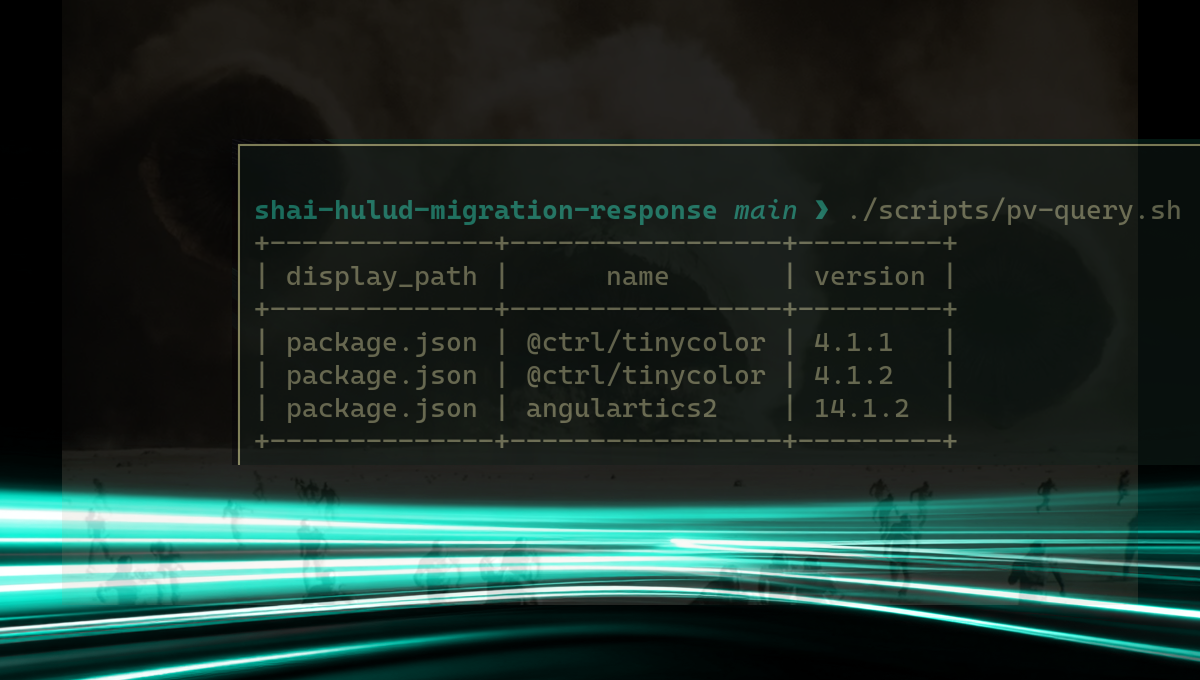
Exposing an MCP server is trivial. Making it useful for AI agents is not. Here's what we learned dogfooding our own tool, and why we built a hosted MCP server backed by real-time open source threat...